GENERAL
road map for a vulnerability management team medium
Introduction to road map for a vulnerability management team medium
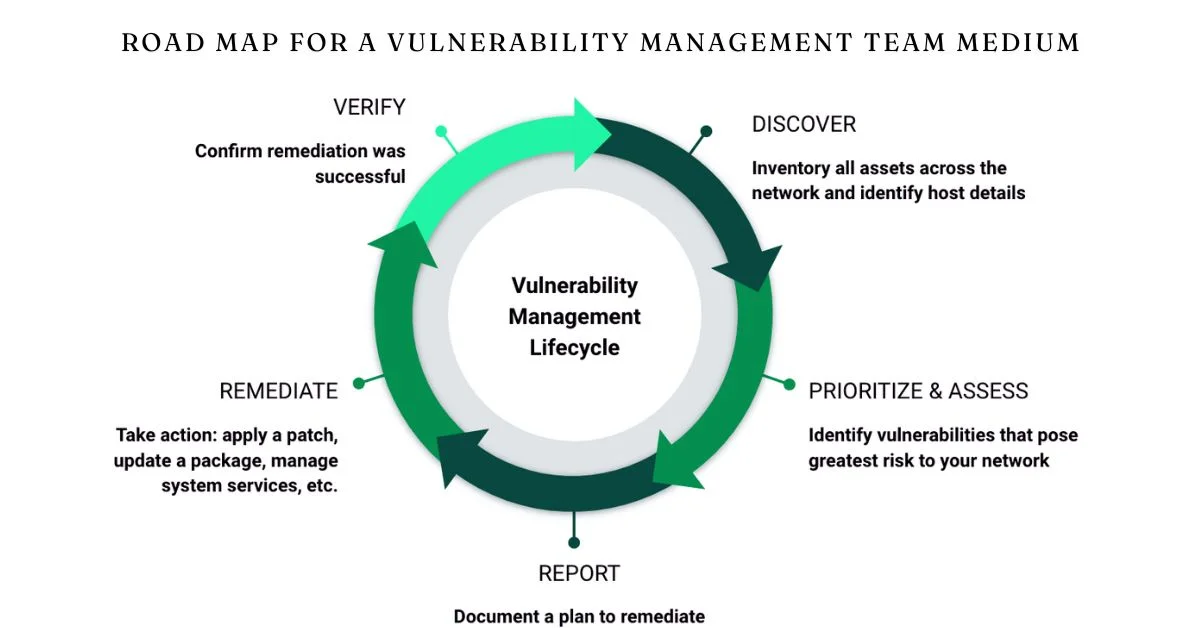
In today’s digital landscape, the importance of a robust vulnerability management team cannot be overstated. As cyber threats evolve and become more sophisticated, organizations must stay one step ahead to safeguard their assets. A well-structured road map for a vulnerability management team medium provides that crucial direction. It lays out clear strategies, responsibilities, and best practices to navigate the complexities of identifying and mitigating vulnerabilities effectively.
Imagine having a detailed plan in place that not only addresses current weaknesses but also anticipates future challenges. This blog post will explore how to develop an effective road map tailored specifically for your team’s needs while enhancing collaboration and communication along the way. Join us as we delve into the key components essential for building an exceptional vulnerability management program that stands resilient against ever-changing threats!
ALSO READ: Predovac: Innovating the Education Landscape
Understanding the Role of road map for a vulnerability management team medium
A well-defined road map for a vulnerability management team medium acts as both a guide and blueprint. It outlines the strategic direction, ensuring everyone understands their roles and responsibilities.
The role of this road map is multifaceted. First, it prioritizes vulnerabilities based on risk levels, allowing teams to focus on what matters most.
This approach helps in resource allocation—ensuring that time and effort target the highest risks rather than spreading resources too thinly across less critical issues.
Moreover, it fosters alignment within the team by setting clear objectives and timelines. This clarity enhances accountability among members while reducing redundancy.
Having a structured plan aids in adapting to new threats or changes within an organization’s infrastructure swiftly. A responsive strategy keeps security measures relevant amidst evolving cyber landscapes.
Key Responsibilities of a Vulnerability Management Team
A vulnerability management team plays a crucial role in safeguarding an organization’s assets. Their first responsibility is to identify vulnerabilities across all systems. This involves continuous scanning, assessing risks, and prioritizing issues based on potential impact.
Next comes remediation. The team collaborates with IT departments to ensure that identified vulnerabilities are addressed swiftly and effectively. They provide guidance on patch management and system updates.
Monitoring is another key task. After remediation, the team must analyze whether fixes have been successful or if further action is necessary.
Reporting also falls under their purview. Regular updates for stakeholders keep everyone informed of the current security posture and any emerging threats.
Training employees about best practices in cybersecurity rounds out their responsibilities, fostering a culture of security awareness throughout the organization.
ALSO READ: Everything about pinterest engineering blog experiments
Developing a road map for a vulnerability management team medium
Creating a road map for a vulnerability management team requires careful planning and strategic thinking. Start by defining the team’s goals. Prioritize what needs immediate attention versus what can be addressed later.
Next, assess your current vulnerabilities and resources. This assessment will inform your team’s capacity to tackle threats effectively. Identify tools that support automation and streamline processes.
Establish clear timelines for each phase of the plan. Short-term milestones build momentum, while long-term objectives keep everyone focused on broader targets.
Involve key stakeholders early in the process to ensure alignment across departments. Regular feedback loops are essential for adapting strategies as new threats emerge or organizational priorities shift.
Document every step taken along this journey. A transparent record not only tracks progress but also helps refine future initiatives.
Best Practices for Implementing and Maintaining a Successful Vulnerability Management Program
Implementing a successful vulnerability management program requires a strategic approach. Start by establishing clear goals and objectives tailored to your organization’s needs. This sets the foundation for effective prioritization.
Regularly schedule scans to identify vulnerabilities across systems, applications, and networks. Consistency is key; these assessments help catch emerging threats early.
Develop a risk-based remediation strategy. Not all vulnerabilities pose the same level of threat, so focus resources on addressing those that could lead to significant damage or data breaches.
Foster an environment of continuous improvement. Encourage feedback from team members and other stakeholders to refine processes over time.
Documentation plays a crucial role in maintaining transparency and accountability within the program. Regular reports can track progress while highlighting areas needing attention.
Invest in training for your team to stay updated on evolving security trends and tools. A knowledgeable team is better equipped to tackle challenges head-on.
ALSO READ: Everything About 2024 duolingo app review medium
Utilizing Automation in Vulnerability Management
Automation plays a pivotal role in modern vulnerability management. It streamlines processes, reducing the burden on team members and allowing them to focus on critical tasks.
By automating routine scans, organizations can quickly identify vulnerabilities across their systems. This rapid detection is vital for maintaining security posture.
Automated reporting tools also enhance visibility. They provide real-time insights into vulnerability status, enabling teams to prioritize remediation efforts effectively.
Integrating automation with existing workflows creates a seamless experience. Tools can be configured to trigger alerts or initiate patching without manual intervention.
Moreover, automation helps mitigate human error—a common pitfall in vulnerability management. By relying on technology for repetitive tasks, teams minimize risks associated with oversight or fatigue.
Leveraging automation empowers teams to respond swiftly and manage vulnerabilities more efficiently while continuously improving overall security measures.
The Importance of Communication and Collaboration within the Team
Effective communication is the backbone of any successful vulnerability management team. When team members share insights and updates, they create an environment ripe for proactive problem-solving.
Collaboration fosters a culture of trust. Team members are more likely to openly discuss vulnerabilities when they feel supported by their peers. This can lead to faster identification and remediation of risks.
Regular meetings can enhance synergy among diverse skill sets within the group. These sessions encourage brainstorming and collective decision-making, essential for tackling complex security challenges.
Utilizing collaborative tools adds further value. Platforms that allow real-time sharing of data help streamline processes and improve response times significantly.
Encouraging open dialogue about successes and setbacks also strengthens team dynamics. It creates learning opportunities that drive continuous improvement in your vulnerability management strategy.
ALSO READ: is medium a good platform for extracurricular activities
Measuring and Reporting on the Effectiveness of Your Vulnerability Management Strategy
Measuring the effectiveness of your vulnerability management strategy is crucial for continuous improvement. Start by defining key performance indicators (KPIs) that align with your organization’s goals. This could include metrics like time taken to remediate vulnerabilities or the percentage of critical issues resolved within a specific timeframe.
Regular reporting should be part of your routine. Share insights with stakeholders through dashboards and reports, emphasizing trends over time rather than just raw numbers. This approach helps highlight areas of success and those needing attention.
Engage team members in discussions about these metrics. Their input can provide valuable context to the data, revealing underlying challenges or successes not immediately visible through numbers alone.
Using an iterative process allows you to adapt and refine strategies based on what works best for your environment. Analyzing feedback regularly fosters a culture of transparency and accountability within the team, ensuring everyone stays aligned toward common security objectives.
Conclusion
Creating a road map for a vulnerability management team medium is crucial in today’s digital landscape. It serves as the backbone for safeguarding an organization against potential threats. By understanding the role of your team and outlining key responsibilities, you set yourself up for success.
Developing this road map requires thoughtful planning and execution. Adopting best practices ensures that your program not only addresses current vulnerabilities but also evolves with emerging threats. Utilizing automation can streamline processes, allowing your team to focus on strategic initiatives rather than manual tasks.
Communication and collaboration within the team enhance effectiveness, fostering an environment where ideas flow freely and challenges are met collectively. Measuring outcomes provides insights into what works well and what needs adjustment.
A well-structured vulnerability management strategy goes beyond just identifying weaknesses; it empowers organizations to take proactive measures against risks while maintaining operational integrity. As you implement these elements, you’ll create a robust defense mechanism that adapts seamlessly to the ever-changing cyber environment.
ALSO READ: Does Medium publish literature reviews? Key insights
FAQs
What is “road map for a vulnerability management team medium”?
A road map for a vulnerability management team medium outlines the strategies, roles, and steps for identifying and addressing cybersecurity risks, ensuring a proactive defense against evolving threats.
Why is a vulnerability management road map essential for cybersecurity?
It provides clear direction, helping teams prioritize vulnerabilities, allocate resources efficiently, and stay aligned with organizational security goals.
What are the key responsibilities of a vulnerability management team?
The team is responsible for identifying vulnerabilities, collaborating on remediation, monitoring fixes, reporting to stakeholders, and training employees on cybersecurity best practices.
How does automation aid in vulnerability management?
Automation streamlines routine scanning, reporting, and patching, enhancing speed, reducing human error, and enabling teams to focus on critical tasks for improved security posture.
How can communication improve vulnerability management outcomes?
Open communication fosters collaboration, accelerates risk identification, and ensures that teams are responsive, informed, and aligned in tackling security challenges effectively.
GENERAL
Boosting Team Morale: Effective Team Building Exercises for Teachers

Feel the energy in the room lift as you see smiles spread across their faces. Imagine a team of educators, united, motivated, and ready to tackle each new day with renewed spirit.
Team building exercises for teachers are the key to this transformation. They spark joy, foster connections, and build a strong foundation of trust.
Ready to explore some fun and engaging activities? Let’s dive in!
Icebreaker Question Circles
Icebreaker question circles are a fantastic way to kick-start teacher teamwork exercises. Teachers form a circle and take turns asking and answering light-hearted questions.
This activity is simple but effective. It helps break down barriers and fosters a sense of camaraderie. The questions can range from fun facts to personal interests, ensuring everyone learns something new about each other.
By engaging in such activities, educators can build stronger bonds. This promotes a positive and collaborative working environment.
Trust-Building Challenges
Trust-building challenges are essential for creating a solid foundation of trust among teachers.
One effective activity is the “Blindfolded Obstacle Course”. In this game, one teacher is blindfolded and must navigate an obstacle course with the help of verbal directions from their partner. This exercise enhances communication and builds trust.
Another engaging activity is “Two Truths and a Lie”. Each teacher shares two true statements and one false statement about themselves. Colleagues must guess which statement is the lie. This game encourages honesty and helps teachers learn more about each other.
School staff unity games can also include the “Human Knot”. Teachers stand in a circle, extend their hands, and grab the hands of others across the circle. The goal is to untangle the knot without letting go of hands.
Creative Problem-Solving Workshops
These workshops present educators with unique challenges that require out-of-the-box solutions. One popular activity is the “Marshmallow Tower”. Teams must build the tallest tower possible using spaghetti, tape, string, and one marshmallow.
Another activity is the “Story Chain”. Teachers sit in a circle, and one person starts a story with a single sentence. This exercise fosters creativity and teamwork. Additionally, it helps educators practice active listening.
For a more complex challenge, consider the “Escape Room” activity. Teachers are locked in a room and must solve various puzzles to escape. Chambers Escape Games offers an excellent venue for such immersive and challenging experiences, ensuring a memorable team-building session.
These workshops harness the power of creative thinking. They provide teachers with the tools they need to inspire their students.
Outdoor Adventure Activities
Outdoor adventure activities serve as fantastic faculty morale boosters. One great activity is a “Nature Hike”. Teachers can explore local trails and enjoy the beauty of nature while bonding.
Another engaging option is “Kayaking”. Paddling together on calm waters helps colleagues communicate and work in sync. It’s a fun way to build relationships.
“Orienteering” is an exciting challenge where teachers use a map and compass to find checkpoints. This activity sharpens problem-solving skills and fosters a spirit of collaboration.
With these activities, teachers can escape the school environment and come together in a new setting. This change of scenery promotes relaxation, rejuvenation, and team bonding.
Benefits of Team Building Exercises for Teachers
Team building exercises for teachers aren’t just about having fun. They build trust, improve communication, and foster strong bonds among educators.
Ready to boost your team’s morale? Start planning your next team building event. Your journey to a stronger, more united team begins today!
Did you find this article helpful? Check out the rest of our blog now!
GENERAL
The Ultimate Guide to Benefits and Features of Pedal Drive Kayaks

Pedal drive kayaks have taken the kayaking world by storm, bringing a whole new level of efficiency and convenience to the sport. Imagine gliding through the water, powered by your legs instead of paddles-it’s a game-changer! These innovative kayaks come equipped with pedals, allowing you to propel forward effortlessly.
In this guide, we’ll dive into the incredible benefits and features of pedal drive kayaks, revealing why they’re becoming a go-to choice for kayak enthusiasts everywhere. Get ready to discover the future of kayaking!
Benefits of Pedal Drive Kayaks
Pedal drive kayaks offer several advantages over traditional paddle kayaks. Let’s take a closer look at some of the most prominent benefits:
Hands-free Operation
One of the biggest selling points of pedal drive kayaks is their hands-free operation. With traditional kayaks, you need to use your arms and paddle continuously to move forward.
This can be tiring and limit your ability to do other things like taking photos or fishing. Pedal drive kayaks free up your hands, allowing you to multitask and enjoy a more comfortable and relaxed kayaking experience.
Increased Efficiency
Pedal drive kayaks are much more efficient than traditional paddle kayaks. This means you can cover longer distances with less effort.
The reason for this is that your leg muscles are larger and stronger than your arm muscles. It allows you to generate more power and propel the kayak forward at a faster pace. This increased efficiency also makes it easier to navigate through strong currents or windy conditions.
Better Maneuverability
Another significant benefit of pedal drive kayaks is their superior maneuverability. The pedals allow for precise and controlled movements. This makes it easier to turn and navigate around obstacles in the water.
This feature is particularly useful when fishing, as you can stay in one spot or move slowly without constantly adjusting your paddle. It’s also great for exploring narrow waterways and tight spaces.
Comfortable Seating
Most pedal drive kayaks come with adjustable seats that provide excellent lumbar support. This makes them much more comfortable than traditional kayaks.
The ergonomic design of the seating also helps distribute weight evenly. This reduces fatigue on longer trips.
Some pedal drive kayaks even have elevated seats. Thus, giving you a higher vantage point for better visibility and improved comfort.
Great for Fishing
Pedal drive kayaks are a game-changer for fishing enthusiasts. The hands-free operation allows you to fish while maintaining your position in the water without constantly paddling.
The increased efficiency also means you can cover more ground and reach fishing spots which would be challenging with a traditional kayak. The maneuverability of pedal drive kayaks also makes it easier to navigate and position yourself for optimal fishing opportunities.
Improved Stability
Pedal drive kayaks have a broader and more stable design compared to traditional kayaks. This makes them ideal for beginners or those looking for a more stable experience.
The wider hull also allows for greater weight capacity. Thus, making it possible to bring along additional gear or supplies on your kayak adventures.
Exercise Benefits
Kayaking is already an excellent form of exercise, but pedal drive kayaks take it to the next level. The constant movement of your legs provides a low-impact and full-body workout.
It’s a great way to improve cardiovascular health, strengthen muscles, and burn calories while enjoying the outdoors. Plus, the hands-free operation allows you to focus solely on the leg movements and get the most out of your workout.
Accessibility for All
Pedal drive kayaks are easier for beginners or those with physical limitations to use. This makes it more accessible to a wider range of individuals.
The hands-free operation and support from the seat make it easier for individuals with arm or shoulder injuries to kayak comfortably. It also allows those with mobility issues to enjoy the sport without feeling limited by their physical abilities.
Features of Pedal Drive Kayaks
Apart from the incredible benefits, pedal drive kayaks also come with a range of features that make them stand out in the kayaking world. Here are some of the most notable features:
Pedal System Types
There are two main types of pedal systems used in kayaks-shaft and rotary. Shaft pedals operate similarly to a bicycle, where your feet push up and down on the pedals.
Rotary pedals work by pedaling in a circular motion, which some users find more comfortable. It’s important to try out both types to see which one works best for you.
Adjustable Pedal Drive System
Pedal drive kayaks come with an adjustable pedal drive system that allows you to customize the position of the pedals for your comfort. This feature is especially useful for individuals with different leg lengths or those who prefer a specific foot placement.
Reverse Functionality
Unlike traditional paddle kayaks, some pedal drive kayaks have a reverse functionality. This means you can move backward by pedaling in reverse, making it easier to navigate tight areas or back out of tricky spots.
Multiple Speed Settings
Most pedal drive kayaks come with multiple speed settings, allowing you to adjust the level of resistance while pedaling. This is especially useful for longer trips when you may need to conserve energy or want a more challenging workout. Motorized kayaks also offer multiple speed settings.
Easy Maintenance
Maintaining a pedal drive kayak is relatively easy, compared to traditional kayaks. The pedals and propulsion system can be easily removed for cleaning and maintenance, ensuring your kayak stays in excellent condition for years to come.
Rudder System
Some pedal drive kayaks also come with a rudder system that helps with steering and tracking. This is particularly helpful in windy or rough conditions, as it provides more control over the kayak’s direction.
Storage Options
Pedal drive kayaks typically have built-in storage options, such as dry hatches, bungee cord rigging, and rod holders. These features make it easier to bring along gear, supplies, and fishing equipment on your kayaking adventures.
Hull Design
The hull design of pedal drive kayaks is different from traditional kayaks. They have a flatter and wider bottom, providing more stability and room for your feet to pedal comfortably.
Rudder and Steering Mechanisms
Pedal drive kayaks have a rudder and steering mechanism that is operated by hand. These features allow for better control and maneuverability of the kayak, making it easier to navigate through different water conditions.
Compatibility with Accessories
Many pedal drive kayaks are designed with compatibility in mind, allowing you to add additional accessories such as fish finders or GPS systems. This makes it easier to customize your kayak to fit your specific needs and interests.
Portability
Despite their larger size, pedal drive kayaks are still portable and easy to transport. Most models can be disassembled or folded down for easier storage and transportation.
Choosing the Right Pedal Drive Kayak
When it comes to choosing the right pedal kayak for sale, there are a few factors to consider. Here are some:
Intended Use
Think about how you plan to use the kayak. Will it primarily be for fishing, recreational use, or touring?
Different pedal drive kayaks have various features and designs that make them better suited for specific activities. For instance, fishing kayaks with pedals may have more storage options and a flatter bottom for stability.
Meanwhile, touring kayaks may be longer and more streamlined for speed. Knowing your intended use will help narrow down your options.
Budget
Pedal drive kayaks can range in price from several hundred to several thousand dollars. Set a budget and research different models within your price range to find the best option for you. Keep in mind that more expensive kayaks may come with additional features and higher quality materials, so it’s important to weigh
Weight and Size
Consider the weight and size of the pedal drive kayak, especially if you plan on transporting it frequently. It’s important to choose a kayak that you can handle comfortably and fits within your transportation capabilities.
Water Conditions
Think about the type of water conditions you will be kayaking in. Some pedal drive kayaks are better suited for calmer waters, while others are designed to handle more challenging conditions.
Test Different Models
It’s always recommended to try out different models before making a purchase. This will help you get a feel for the different features and determine which one works best for you.
Safety Tips for Pedal Drive Kayaking
While pedal drive kayaks have many benefits, it’s essential to follow safety precautions when using them. Here are some tips to keep in mind:
- Always wear a life jacket
- Learn kayak features first
- Check conditions before kayaking
- Carry first aid kit
- Hydrate and bring snacks
- Inform route and return
Experience the Benefits and Features of Pedal Drive Kayaks Now!
Pedal drive kayaks offer a range of benefits and features that make them an attractive choice for kayak enthusiasts. From hands-free operation to superior maneuverability, these kayaks provide a more efficient and comfortable experience on the water. With various models and options available, there’s a pedal drive kayak out there for everyone. So why not give it a try and discover the future of kayaking for yourself? Happy paddling!
Is this article helpful? Keep reading our blog for more.
GENERAL
The Essential Private Caregiver Job Responsibilities for Senior Patients

Caring for senior patients is a profoundly rewarding yet demanding role, requiring a blend of compassion, skill, and dedication.
Private caregivers play a crucial part in ensuring that elderly individuals maintain their dignity, independence, and quality of life.
This article explores the essential responsibilities of a private caregiver job, highlighting the key aspects that contribute to effective and compassionate senior care.
Introduction to the Private Caregiver Job
A private caregiver job involves giving personalized help to senior patients. The help includes aiding with daily activities and healthcare. This role is pivotal. It helps elderly people live comfortably and safely in their own homes. It fosters their independence and well-being.
Private caregivers have many duties. They go beyond just physical care. They also include emotional support, companionship, and advocacy.
Personal Hygiene and Grooming
One of the main jobs of a private caregiver is helping senior patients. They help with personal hygiene and grooming. This includes helping with bathing, dressing, and grooming tasks such as brushing hair and teeth. Good hygiene is crucial for preventing infections. It also ensures the well-being of the senior.
Mobility and Exercise
Ensuring that senior patients remain as active as possible is another critical aspect of the private caregiver’s job. Caregivers assist with mobility. They help patients:
- move around the house
- do exercises
- do physical activities
These activities enhance their strength and flexibility. This not only promotes physical health but also boosts mental well-being.
Medication Management
Managing medications is a vital responsibility for private caregivers. This involves ensuring that seniors take their medications on time and in the correct dosages.
Caregivers often work with healthcare providers. They do this to manage prescriptions, watch for side effects, and change medications as needed.
Meal Preparation and Nutrition
Good nutrition is vital for senior health. Private caregivers often plan and cook meals. This includes preparing balanced meals that meet diets and preferences. You must also assist with feeding if needed. And, you must ensure that the patient stays hydrated.
Light Housekeeping
Maintaining a clean and safe living environment is another important duty of a private caregiver job. This includes tasks such as:
- cleaning
- laundry
- organizing the home
They prevent accidents and make a comfy space for the senior.
Errands and Transportation
Private caregivers frequently assist with running errands and providing transportation for senior patients. This includes:
- grocery shopping
- picking up prescriptions
- driving patients
Ensuring that seniors can attend appointments and stay socially active is vital for their overall well-being.
Vital Signs and Health Monitoring
Monitoring the health of senior patients is a critical component of a private caregiver job. Caregivers regularly check vital signs. These signs include:
- blood pressure
- heart rate
- temperature
They also watch for any changes in the patient’s condition. Early detection of health issues allows for timely intervention and medical attention.
Coordination with Healthcare Providers
Private caregivers often act as liaisons between senior patients and healthcare providers. They talk to doctors, nurses, and other medical professionals.
They do this to ensure that the patient’s health needs are being met. This includes scheduling appointments, following up on medical instructions, and advocating for the patient’s health and well-being.
Emergency Response
Being prepared to respond to emergencies is a crucial aspect of the private caregiver job. Caregivers need to be trained in basic first aid and CPR, and they must know how to act quickly and effectively in case of an emergency. This preparedness can make a significant difference in the outcome of a health crisis.
Companionship
Providing companionship is a key responsibility in the private caregiver job. Senior patients often face loneliness and isolation, which can lead to depression and anxiety. Caregivers offer emotional support. They also do activities that promote social interaction, like:
- playing games
- watching movies
- having conversations
Mental Stimulation
Keeping senior patients mentally stimulated is essential for maintaining cognitive health. Caregivers engage patients in activities that challenge their minds. These include puzzles, reading, and hobbies that the senior enjoys. This not only keeps the brain active but also enhances the patient’s quality of life.
Emotional Support
Emotional well-being is as important as physical health in senior care. Private caregivers provide a listening ear, offer encouragement, and support seniors through difficult times. Building a trusting relationship with the patient is crucial. So is being empathetic. It’s key for effective caregiving.
Dementia and Alzheimer’s Care
Caring for patients with dementia or Alzheimer’s disease requires specialized skills and knowledge. Private caregivers need to understand the unique challenges of these conditions. They include:
- memory loss
- confusion
- behavioral changes
Providing a safe and supportive environment is essential for managing these patients effectively.
Palliative and Hospice Care
For seniors with terminal illnesses, private caregivers often provide palliative or hospice care. This involves managing pain and symptoms. It also involves offering comfort and supporting the patient and their family through the end of life. Compassion and sensitivity are paramount in this aspect of caregiving.
Rehabilitation Support
Senior patients recovering from surgeries or illnesses may need rehabilitation support. Private caregivers help with physical therapy. They also watch progress and encourage patients to follow their rehab plans. This support is crucial for the patient’s recovery and return to independence.
Confidentiality
Keeping patient’s personal and medical information confidential is a core duty of a private caregiver. Caregivers must follow the law and ethics. They must protect sensitive information and only share it with authorized people.
Respect for Patient Rights
Respecting the rights and autonomy of senior patients is essential in caregiving. This includes honoring their preferences and decisions, even when they differ from the caregiver’s own views. Empowering seniors to make choices about their care promotes dignity and self-worth.
Advocacy
Private caregivers often act as advocates for their patients. They ensure patients get the needed care and services. This includes navigating healthcare systems. It means accessing community resources and standing up for the patient’s rights. Advocacy is a critical role that enhances the quality of senior care.
The Heart of a Private Caregiver Job
The private caregiver job is crucial for senior care. It covers various tasks to ensure the well-being of elderly people. They help with daily activities and watch their health. They also offer emotional support and specialized care. Private caregivers are key to a caring and efficient system.
By doing these duties, caregivers can truly impact seniors’ lives. They help them live with dignity, independence, and happiness.
Looking for more valuable tips and guides? Our blog offers a wealth of information on various topics that can help.

 HOME IMPROVEMENT1 year ago
HOME IMPROVEMENT1 year agoThe Do’s and Don’ts of Renting Rubbish Bins for Your Next Renovation

 BUSINESS1 year ago
BUSINESS1 year agoExploring the Benefits of Commercial Printing

 HOME IMPROVEMENT10 months ago
HOME IMPROVEMENT10 months agoGet Your Grout to Gleam With These Easy-To-Follow Tips

 HEALTH11 months ago
HEALTH11 months agoThe Surprising Benefits of Weight Loss Peptides You Need to Know

 TECHNOLOGY1 year ago
TECHNOLOGY1 year agoDizipal 608: The Tech Revolution Redefined

 BUSINESS1 year ago
BUSINESS1 year agoBrand Visibility with Imprint Now and Custom Poly Mailers

 HEALTH10 months ago
HEALTH10 months agoYour Guide to Shedding Pounds in the Digital Age

 LAW2 years ago
LAW2 years ago7 Key Questions to Ask When Hiring a Criminal Lawyer










