BUSINESS
Securing Business Process Automation: IT’s Role in Protecting Automated Workflows

As businesses increasingly turn to automation to streamline their processes, improve efficiency, and reduce costs, the security of these automated workflows becomes a critical concern. Business Process Automation (BPA) involves the use of technology to automate repetitive tasks and complex workflows, often integrating with various systems and handling sensitive data. While BPA offers significant advantages, it also introduces new security challenges that must be addressed to protect the integrity and confidentiality of automated processes. It is crucial to secure these computerized workflows, ensuring businesses reap automation’s benefits without compromising security. This article explores the critical security risks associated with BPA and how IT can effectively mitigate them.
1. Identifying Security Risks in Business Process Automation
“Before implementing security measures, it’s crucial to understand the potential risks that Business Process Automation (BPA) can pose, particularly when sensitive data is involved,” says Gemma Hughes, Global Marketing Manager at iGrafx, a leading company specializing in business process management solutions. “Automated workflows often handle critical information, such as customer data, financial records, and proprietary business details. These workflows can become prime targets for cyberattacks without proper security measures, resulting in data breaches, financial losses, and severe reputational damage. Common security risks in BPA include unauthorized access, data leaks, system vulnerabilities, and exploiting automated processes by malicious actors.”
Hughes emphasizes that IT teams must conduct comprehensive risk assessments to identify potential vulnerabilities within automated workflows. “This process involves evaluating the security of the automation tools in use, analyzing the integration points with other business systems, and scrutinizing data flows within the automated processes. By clearly understanding where the vulnerabilities lie, IT teams can develop targeted strategies to mitigate these risks and safeguard the organization’s operations,” she adds. At iGrafx, the focus is on creating secure business processes that enhance efficiency and protect valuable assets from emerging threats, ensuring that businesses can fully leverage automation without compromising security.
2. Implementing Robust Security Measures for Automated Workflows
“Once the security risks have been identified, IT teams must implement robust security measures to safeguard automated workflows,” says Tim Parker, Director at Syntax Integration. “One of the foundational steps is to ensure that access to automation tools and systems is tightly controlled. This involves deploying multi-factor authentication (MFA), role-based access control (RBAC), and strict user permissions, which limit access to only those individuals who require it for their specific roles. By managing access effectively, IT support teams can significantly reduce the risk of unauthorized access to sensitive automated processes.”
Parker also highlights the importance of keeping automation tools and integrated systems up to date with the latest security patches and software updates. “Regular updates help close vulnerabilities that attackers might exploit, making it a critical task for IT support teams,” he explains. “Additionally, encrypting data both at rest and in transit is essential, as it ensures that even if data is intercepted, it remains unreadable to unauthorized parties.”
Another crucial measure, according to Parker, is the implementation of comprehensive logging and monitoring systems. “By continuously monitoring automated workflows in real-time, IT support teams can detect unusual activity or potential security incidents early on,” he notes. “Setting up automated alerts allows IT to respond swiftly to suspicious behavior, mitigating risks before they escalate and ensuring that business operations remain secure and uninterrupted.” Syntax Integration’s approach emphasizes a proactive stance on security, where ongoing monitoring and quick response capabilities are integral to protecting business processes.
3. Establishing a Proactive Security Culture within the Organization
“While technical measures are critical, fostering a proactive security culture within the organization is equally essential for protecting automated workflows,” says Adam Crossling, Marketing & New Business Director at zenzero. “IT teams need to work closely with other departments to ensure that security is a core component at every stage of the automation lifecycle, from the initial design and development phases to deployment and ongoing maintenance. This collaboration helps embed security into the fabric of the organization’s operations.”
Crossling emphasizes the importance of regular security training for employees to raise awareness of best practices and the potential risks associated with automation. “Security isn’t just an IT issue; it’s a company-wide responsibility. Regular training sessions help employees understand their role in maintaining security, from recognizing phishing attempts to following protocols for handling sensitive data within automated systems,” he explains.
Furthermore, IT should establish clear policies and procedures for managing security incidents related to Business Process Automation (BPA). “Having a comprehensive incident response plan in place is crucial,” Crossling adds. “This plan should clearly outline the steps to be taken in the event of a security breach, including immediate containment measures, communication protocols with stakeholders and regulatory bodies, and steps for recovery. By adopting a proactive approach to security, businesses can significantly reduce the impact of potential incidents, maintain operational continuity, and uphold trust with their customers and partners.” At Zenzero, the focus is on integrating security into the core of IT support services, ensuring businesses can leverage automation confidently and securely.
Conclusion
Securing business process automation is a critical responsibility for IT teams, as it ensures that security threats do not undermine the benefits of automation. IT can effectively protect automated workflows by identifying and addressing the security risks associated with BPA, implementing robust security measures, and fostering a proactive security culture within the Organization. As automation continues to play an increasingly important role in business operations, securing these processes cannot be overstated. By taking a comprehensive approach to security, businesses can confidently leverage BPA to drive efficiency and growth, knowing that their automated workflows are well-protected against potential threats.
BUSINESS
Unlock the Secret to a Successful Pay Review (Hint: It’s Not Just About Money)

We’ve all been there, haven’t we? The dread of another annual pay review cycle creeping up on the calendar. The idea of the pay review process immediately conjures up thoughts of a stack of paperwork, seemingly endless meetings, and the nagging feeling you’re playing catch-up to market rates and may be getting things wrong.
But what if we told you that pay reviews don’t have to be a soul-sucking HR ritual? They can actually be a golden opportunity to show your employees you care, boost morale, and even improve your bottom line.
Why Pay Reviews Matter (More Than You Think)
Let’s be completely honest for a minute: money talks. A fair and transparent pay review process sends a powerful message to your staff that you value their hard work and want to invest in their future. It’s not just about the numbers, it’s about showing appreciation for their efforts, fostering loyalty, and perhaps most importantly of all, retaining your top talent.
The Benefits of a Stellar Pay Review Process
- Happier Employees, Happier You: When employees feel valued and fairly compensated, they’re more engaged, productive, and less likely to jump ship. That means a happier, more stable workforce – and less stress for you!
- Outsmart the Competition: A structured pay review process helps you stay on top of market trends and make sure your salaries remain competitive. That’s crucial for attracting and retaining top talent in a tough market.
- Motivate and Retain: Regular pay reviews can be a powerful motivator, encouraging employees to go the extra mile throughout the year knowing their efforts will be recognized and rewarded.
- Transparency Builds Trust: A clear and open pay review process fosters trust and strengthens the relationship between employees and management.
Your Pay Review Cheat Sheet: Best Practices That Work
Okay, enough with the “why” – let’s get into the “how.” Here’s your step-by-step guide to making pay reviews less of an annual headache and more of a New Year win:
Plan Ahead, Way Ahead
Don’t wait until the last minute to scramble. Set a clear timeline for your pay reviews, communicate it to your staff, and stick to it. This avoids nasty surprises and gives everyone time to prepare.
Data is Your Friend
Don’t rely on gut feelings or outdated spreadsheets. Use reliable market data (savvy HR teams even use tools like Figures.hr for this!) to benchmark your salaries against industry standards.
Transparent is Terrific
Be open and honest about your compensation philosophy. Don’t just share proposed numbers with employees, explain how pay decisions are made, what factors are taken into account, and how performance is measured.
Communication is Key
Encourage an open dialogue throughout the process. Let employees know they have a voice and their opinions are valued. This builds trust and makes for a smoother review process.
Individualised is Best: Everyone’s different, right? Tailor your pay reviews to each employee’s role, experience, and performance. A one-size-fits-all approach simply won’t cut it.
Don’t Forget the Non-Monetary
Remember, it’s not always about the money. Consider additional benefits, training opportunities, or flexible working arrangements as part of the overall package.
Feedback Loop
After each pay review, take time to reflect. What went well? What could be improved? Use this feedback to refine your process for next time.
Making Pay Reviews Work for You
With a bit of planning and a human touch, annual pay reviews really can go from a dreaded chore to a powerful tool for boosting employee engagement, improving morale, and keeping your business competitive. It’s an investment in your people and, ultimately, your company’s success.
If you’re looking for a way to streamline your pay reviews and make them more data-driven, consider exploring compensation management software. Providers like Figures.hr offer a suite of tools designed to simplify the process, improve accuracy, and ensure your pay decisions are informed and fair.
Software to the Rescue: How It Streamlines Your Pay Reviews
Okay, let’s face it. Even with the best intentions, managing pay reviews manually can be a real drag. That’s where compensation management software swoops in like a superhero.
Here’s how it can save you time, stress, and maybe even a few tears:
Data at Your Fingertips
Say goodbye to endless spreadsheet juggling! The right software puts all your compensation data in one place, making it easy to access, analyse, and compare. No more digging through files or hunting down outdated information.
Market Data on Demand
Remember that bit about staying competitive? Compensation software like Figures.hr plugs you into real-time market data, so you can instantly benchmark your salaries against industry standards. No more guesswork or worrying you’re lagging behind.
Customisable Salary Structures
Forget one-size-fits-all. With the right software, you can build salary models tailored to your company’s unique needs. Factor in everything from job roles and experience to performance ratings and regional variations.
Scenario Planning Made Simple
Ever wonder how a promotion or a market shift might impact your budget? Compensation software lets you run “what if” scenarios and forecast future costs, so you’re always prepared.
Automate the Tedium
Who loves paperwork? (No one, that’s who!) Compensation software automates tedious tasks like data entry, calculations, and even approval workflows. That frees up your time to focus on what really matters: satisfying your people.
Transparency for All
Some platforms even offer tools for sharing compensation information with employees in a clear and understandable way. This boosts trust and helps everyone feel like they’re on the same page.
Making the Switch: Tips for Choosing the Right Software
Okay, so you’re sold on the idea of software, but where do you start? Here are a few tips:
- Know Your Needs: What are your pain points? What features are must-haves? Start by identifying your company’s specific needs and priorities.
- Do Your Research: Not all compensation management software is created equal. Read reviews, compare features, and ask for demos to find the best fit for your company.
- Think Long-Term: Choose a platform that can grow and evolve with your business. Look for flexibility and customization options.
- Support Matters: Make sure the software provider offers excellent customer support. You want to know that you’ll have help when you need it.
Ready to Take the Plunge?
Investing in compensation management software is an investment in your people and your company’s future. It’s a way to ditch the outdated practices, embrace a modern mindset, and build a pay strategy that truly works for everyone. So, are you ready to say goodbye to spreadsheet nightmares and hello to a brighter, happier pay review process? Taking the time to research – and then implement – compensation management software will almost certainly be time (and money) very well spent.
One caveat as we close, though: While software can be a game-changer, it’s not a magic wand. You still need to put in the effort to build a fair, transparent, and motivating compensation strategy. But with the right tools and the right mindset, you can turn the often dreaded annual pay review process into a positive experience that benefits everyone.
BUSINESS
Best-Selling Website Templates: Cool, Foolproof Tools for Us Non-Coder Folks
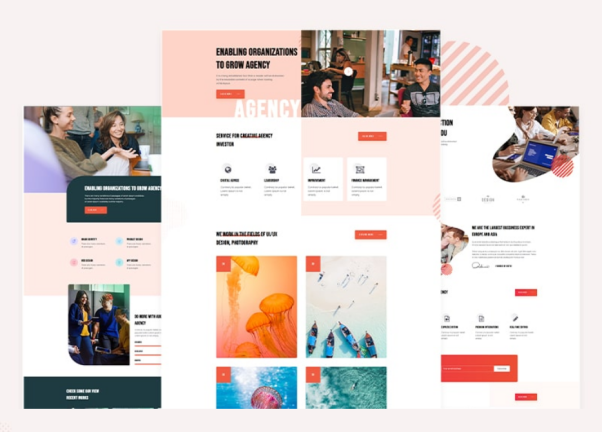
Let’s be real, trying to build a whole website on your own when you’re not good at coding is pretty much the worst. Unless you want to pull your hair out, it’s just not a battle worth fighting for us non-techy folk.
Here’s where website templates come in as a breakthrough. These pre-built web designs are a lifesaver for regular people who want a fresh, modern site without the cold sweats of coding nightmares.
In this post, I’ll break down some of the most popular providers offering the best-selling website templates on the market. For anyone who’s a small business owner, blogger, photographer, or just wants a slick personal site, these themes will provide you with the necessary tools. And won’t require any hardcore tech skills instead. Let’s dive in!
TemplateMonster: The Web Template Juggernaut
In terms of best-selling website templates, TemplateMonster is an absolute titan that should be at the top of your list. These guys have been dominating the web design game for ages with a downright massive library.
No matter what kind of site you’re trying to build – for a hip new restaurant, an online clothing store, a photography portfolio, or even just a personal blog. TemplateMonster provides tons of fresh, modern web themes for various needs. Their collection is stacked with thousands upon thousands of options across all kinds of industries and niches.
But here’s the real kicker that makes this marketplace so clutch for us non-techies. Their themes are easy to customize, even if you don’t know a lick of code. Furthermore, most designs are intuitive with smart editors, so it’s easy for us to effortlessly tweak layouts, colors, fonts, and more. It’s all visual and straightforward as can be.
On top of this user-friendly aspect, the platform has six-month customer support, while vendors provide extensive documentation to handhold you through any hiccups.
The Other Big Kahunas of Best-Selling Webpage Layouts
Of course, while TemplateMonster may be royalty, they aren’t the only players in town. A few other major heavyweights in this space deserve some cheers.
- Take Wix, for instance – their whole platform is about making website building an absolute cakewalk. Even for folks who wouldn’t know HTML from a hole in the ground. With Wix’s drag-and-drop interface and tons of pre-built web layouts, just about anyone can get a pretty snazzy site up and running in no time flat. Their best-selling website templates cover the essentials like online stores, booking platforms, portfolios, and more. Plus, making customizations is as easy as arranging digital Lego blocks.
- Then you’ve got the sleek, professional stylings of Squarespace’s best-selling demo collection. Their solutions are drool-worthy if you want your page to have a super clean, modern, art gallery type of vibe. Even though Squarespace is a little pricier than some other options, their designer-made templates have that polish to give any online presence a first-class and high-end look. If you crave a luxe, minimalist aesthetic, Squarespace has your back.
- We’d also fail to give a shoutout to the OG of the website world – WordPress. This content management system has been around forever and remains wildly popular for small businesses, bloggers, and almost any kind of web page. The beautiful part about WordPress is the sheer number of best-selling options available. Many of which are even free or stupidly cheap.
Between giants like Wix, Squarespace, WordPress, and the aforementioned TemplateMonster, anyone can find gorgeous, user-friendly, and even feature-rich webpage layouts. What they also have in common is that you don’t have to pound your head on the keyboard trying to code something from scratch.
Why TemplateMonster Deserves Another Mention
Alright, let’s circle back around to TM because they do deserve some extra love here. While I’ve highlighted some other awesome digital asset providers, these guys still stand out as an elite option worth your hard-earned dollars.
- First off, the company has the best-selling templates available for basically any budget. No matter your status – a big business owner or a bootstrapped blogger just starting. You’ll find affordable designs that punch way above their weight class. From dirt-cheap basics to premium packages loaded with extras, there’s something for every price point.
- Speaking of extras, their best-selling items come packed with quality-of-life features like SEO readiness and built-in mobile responsiveness right out of the box. Forget about clunky monstrosities that look janky on smartphones and aren’t up to search engine standards. TM prioritizes modern web rules.
- Moreover, they offer tons of optional goodies to level up your online game even further. Need professional stock photos or graphics? They gotcha. Looking for web hosting to make your life easier? It’s available. Want some extra paid customization services to personalize your site? Hey, they got you.
The bottom line is that TemplateMonster goes far beyond just basic templates. It’s a whole ecosystem with just about everything you could need to spin up a gorgeous, top-performing online presence.
My suggestion? Just head over to their marketplace and look around. Get a first-hand feel for their huge collection of best-selling products across all categories. I’m ready to put money on you to find something that catches your eye!
In Conclusion
To wrap things up, let’s recap the main selling point of website templates. In my opinion, they’re the most convenient way to launch a slick, professional-looking webpage without any time- or money-consuming work.
With a quality design as your foundation, everything is pre-built and ready to go. All you have to do is customize some surface-level stuff like colors, images, text, etc. It’s a phenomenally easy way to get an awesome online presence up and running in essentially no time at all.
If I were you, I’d stop procrastinating and delaying my website dreams. Take advantage of the multitude of user-friendly, code-free themes out there from reputable providers. Your new blog or store is just a few clicks away!
BUSINESS
Cohort Tracking for B2B Audience Attribution Accuracy

A million-dollar question is: how can we prove paid advertising ROI? Most advertisers realize the complexity of the B2B customer journey: the sales opportunities might come from the organic search or outbound emails, but they’ve likely seen your ads before.
Fair enough, most teams prefer sticking with the last-click conversion to attribute campaign ROI to the corresponding ad channel. However, it doesn’t explain whether the increased ad spend impacted your overall marketing ROI and contributed to final revenue. Everything changes when you leverage an audience-based attribution model known as cohort tracking.
What Is the Ad Audience Cohort Tracking?
The audience-based attribution model called cohort tracking allows you to identify a converted lead as a member of your ad audience segment. Thus, you can conclusively say that the customer has seen your ad, and it has influenced their purchase decision.
Knowing who was in the ad audience segment and how many sign-ups you got during the active paid ad campaign allows you to attribute conversions from organic and direct visits to your advertising efforts. Just like that, it’s crystal clear and spares you from over-complicated attribution systems.
Most importantly, such a transparent multi-channel attribution helps the marketing team justify additional ad budgeting.
How Cohort Tracking Differs from the Last-Click Attribution
The prime benefit of switching to an ad audience cohort tracking system is that it allows you to oversee ad performance holistically and analyze it beyond the last-click conversion. You no longer rely on campaign-specific UTM parameters to measure advertising success.
Advertising based on lookalikes and the platform’s native targeting doesn’t allow you to access the actual identifiers of ad network members, which you can use to match converted leads with your CRM or B2B IP tracking. This means you can’t determine how many inbound prospects converted after seeing your messages, which could be quite valuable for your ABM efforts in the future. The only metric you can gauge in this case is last-click conversion ROI. The typical measurement pattern includes:
- Tracking UTM link clicks.
- Counting lead form fill-outs.
- Attributing lead conversions to the campaign you ran.
- Calculating customer acquisition costs (sales and marketing spend/customers acquired) and lifetime value.
Conversely, cohort audience tracking allows you to calculate ROI regardless of the traffic source, as you can count the conversion rate for the entire pre-defined audience segment.
How Ad Measurement Changes with Audience-Based Tracking
The point is that you complement the existing last-click tracking with additional data on the audience to which you serve ads. It adds accuracy when attributing newly acquired MQLs/SQLs to the recently run advertising campaigns.
This enhanced attribution approach will bring together tracking data coming from:
- Ad platform analytics. You can analyze which part of the audience was reached during the active campaign and how many of them were engaged with the ad message and clicked through.
- IP Targeting and Reverse IP lookup. With IP targeting, you can deliver relevant messages to IPs, while the reverse IP lookup helps to identify incoming traffic from an ad platform and match visits with third-party prospecting data provided by B2B data vendors.
- UTM links. Clicked-through UTM links will flag platform-specific traffic and show how it is distributed within your multi-channel campaign.
- Emails/Names. You can cross-match acquired MQls/SQLs’ contact data with the audience list uploaded to the ad platform.
Eventually, you get the most accurate attribution of converted leads to your PPC campaign. This enables you to effortlessly calculate multi-channel ROI and identify the top revenue-contributing channels.
Leverage Custom List-Based Audiences to Unlock Cohort Tracking
The cohort tracking will work out only if there’s a high enough match rate (>70%) between ad network accounts and your list-based audience. The problem is that, on average, you have a contact name, business email, and work phone number in a targeted list record. With such scarce prospecting data in hand, you can’t expect match rates higher than 10 to 30%.
Enable B2B customer data enrichment, and you’ll ramp up ad platform match rates. By enriching customer records through Primer and similar B2B data orchestration platforms, you can achieve 70-80% matching for custom-built audiences across Facebook, LinkedIn, Instagram, Google Ads, and other PPC networks.
Moreover, Primer allows you to build custom audiences as close as possible to your Ideal Customer Profile and synch them across channels. Start with targeted paid social campaigns and then run an automated email follow-up campaign on the same leads group. Such a combined approach can grow your conversion rate by another 20%+.
Simplified Pursuit of ABM Accounts
Let’s not forget that cohort tracking can greatly boost the efficiency of strategic account-based marketing. Since you’re serving targeted ads to pre-qualified audiences, the overall cost of customer acquisition drops dramatically.
Additionally, you can effectively identify highly engaged leads, attribute higher scores to them, and pursue them as high-value accounts. Audience-based attribution allows you to double down on these valuable leads by streamlining multi-channel follow-ups.

 HOME IMPROVEMENT1 year ago
HOME IMPROVEMENT1 year agoThe Do’s and Don’ts of Renting Rubbish Bins for Your Next Renovation

 BUSINESS1 year ago
BUSINESS1 year agoExploring the Benefits of Commercial Printing

 HOME IMPROVEMENT10 months ago
HOME IMPROVEMENT10 months agoGet Your Grout to Gleam With These Easy-To-Follow Tips

 HEALTH10 months ago
HEALTH10 months agoThe Surprising Benefits of Weight Loss Peptides You Need to Know

 TECHNOLOGY1 year ago
TECHNOLOGY1 year agoDizipal 608: The Tech Revolution Redefined

 HEALTH10 months ago
HEALTH10 months agoYour Guide to Shedding Pounds in the Digital Age

 BUSINESS1 year ago
BUSINESS1 year agoBrand Visibility with Imprint Now and Custom Poly Mailers

 LAW1 year ago
LAW1 year ago7 Key Questions to Ask When Hiring a Criminal Lawyer









