APPS & SOFTWARE
The Best 8 Voice Changer for PC and Online
HitPaw Voice Changer

Looking for the best voice changer for gaming, livestream, or live calls? There are two main changers that you will find on the internet which are online or pc program-based. The online voice changer allows users to change their voice without installing any program. On the other hand, the PC-based voice changers have to be installed on the system. By installing a voice changer on a PC you get advantages such as more features like changing voice in real time on other installed programs such as games. This article will guide you on the best voice changers for PC or online.
Part 1. The Best Voice Changer for PC
HitPaw Voice Changer
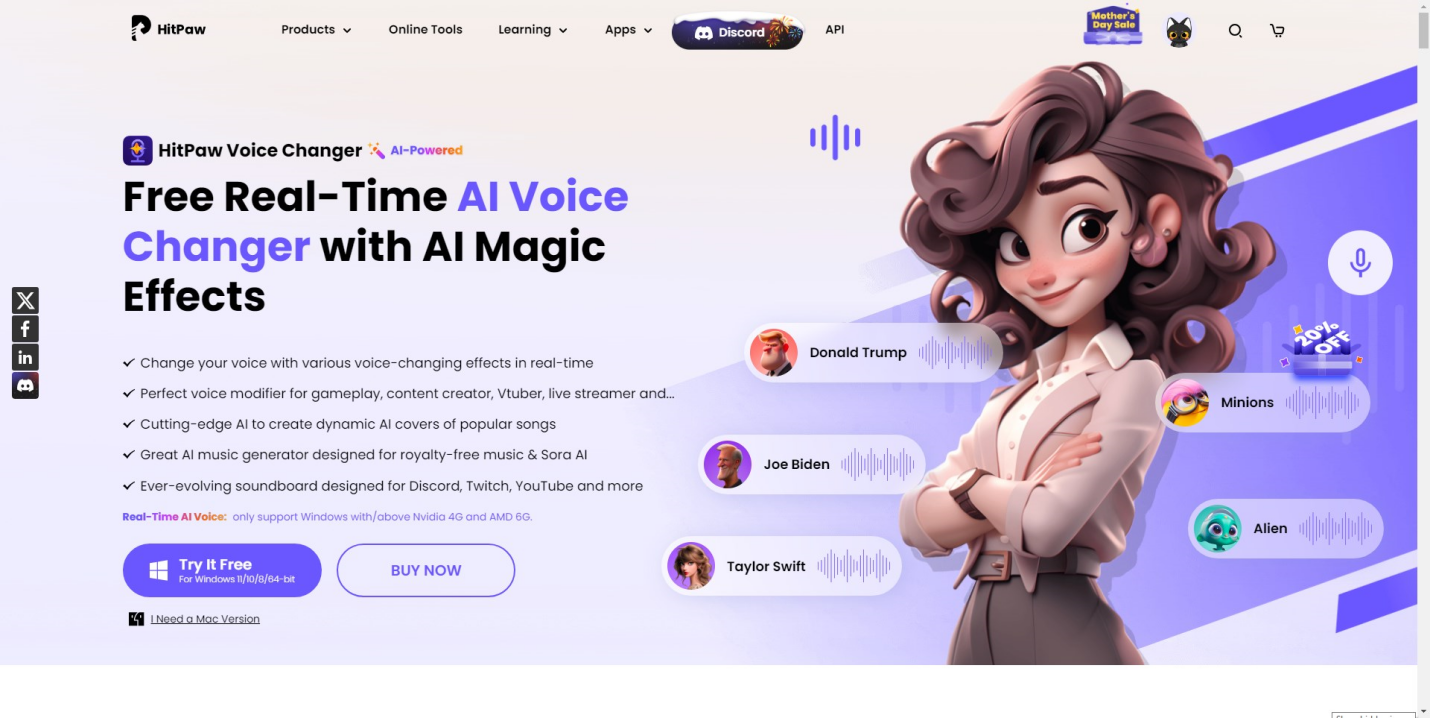
HitPaw Voice Changer is one of the most advanced voice changers for PC and Mac. It features cutting edge AI that allows users to enjoy over 500 voice effects of popular celebrities. The library continuously expands as new voices are added every month. Apart from changing voice Hitapaw also allows users to create custom AI background music. It also comes with a soundboard for livestreaming platforms such as Twitch, Discord, YouTube and many others. Lets take at lookat some of its features.
key features
Free to use: You can download and use the software without paying anything. There might be limitations in the free version compared to paid plans, but it allows you to try out the basic features.
Personalize the voice changer for the PC: Users can set hotkeys on their keyboards to switch to different voices fast during live streams, gaming, or live calls.
Real time voice changer: The best thing about Hitpaw is that you can change your voice in real time. It does all this while utilizing minimalcpu resources
Very beginner-friendly: Hitpaw Voice Changer is designed to be easy to use, even for people with no prior experience with audio editing software.
Various voice characters: It comes with a huge library of character voices from artists, to actors that is continuously updated with more every month.
Other voice changers for PC
MorphVoc
MorphVox is a well-regarded voice changer known for its user-friendly interface and vast library of voice modification options. Perfect for beginners and experienced users alike, MorphVox offers a variety of pre-programmed voices that can instantly transform your voice into a robot, alien, or even make you sound like the opposite gender.
Features
Preset voices: MorphVox offers a wide range of pre-programmed voices like robot, alien, and male-to-female.
Voice creation tools: Allows you to fine-tune existing presets or create custom voices by adjusting pitch, formant (resonance), and effects.
Soundboard: This lets you add sound effects to your voice alongside the voice modification.
Voicemeeter
Voicemeeter is more than just a voice changer; it’s a powerful audio mixing application with built-in voice manipulation capabilities. It provides extensive control over your computer’s audio inputs and outputs, allowing you to mix and manipulate sounds from your microphone, games, and other applications with incredible precision.
Features
Advanced audio routing: Offers extensive control over your computer’s audio inputs and outputs, allowing you to mix and manipulate multiple audio sources.
Voice effects: Provides basic voice modification features like pitch shifting and EQ. (Equalization – adjusting different frequency ranges)
VST support: Lets you integrate additional virtual instruments or effects plugins (VST) for more advanced voice manipulation (Requires additional software purchase).
MagicMic
MagicMic is a user-friendly voice changer designed specifically for streamers and content creators who want to add excitement and entertainment to their broadcasts. Streamlining the process for live voice modification, MagicMic offers a variety of voice filters and effects that can be applied in real time while you’re streaming or recording.
Features
Real-time voice effects: Offers a variety of voice filters and effects that can be applied live while streaming or recording.
Voice library: Provides access to a collection of pre-recorded voices and sound effects.
Voice morphing: Allows you to blend your voice with different characters or sound effects for unique audio combinations.
Clownfish

Clownfish offers a basic set of voice modification tools that can still add a fun element to your audio projects. It allows you to adjust the pitch of your voice to sound higher or lower, and add echo effects for a more dramatic touch. Clownfish also comes with a basic voice recording function, so you can capture your voice with the applied effects and share it with others.
Features
Voice effects: Offers voice modification options like pitch shifting and echo.
Voice recording: This allows you to record your voice with the applied effects.
Customization options: While limited, it lets you adjust some parameters of the voice effects.
Part 2. The Best Voice Changer for Online
Voicechanger.io
Voicechanger.io is a free online tool that lets you modify your voice recordings. You can use it to change the pitch of your voice, making it sound higher or deeper, or add effects like making it sound like a child, robot, or even Donald Duck. It’s a simple tool for having fun with your voice or potentially anonymizing it for short recordings.
Media.io Online Voice Changer
Media.io offers an online voice changer that utilizes AI technology. You can upload audio or video files and modify the voices within them. This tool allows for pitch adjustments, potentially creating subtler or more dramatic vocal transformations. There’s also the option to explore various voice effects.
Murf

Murf.Ai steps beyond basic voice changing, offering an AI-powered text-to-speech experience. Instead of modifying existing recordings, you provide your script and Murf.Ai generates a voiceover from scratch. With a library of diverse voices in multiple languages and accents, you can pick the perfect tone to match your project.
Conclusion
You can change your voice to sound like your favorite movie character, artist, or celebrity. To achieve this you need a voice changer for PC or one that is online based. Each of these two options has its own advantages. If you are looking for the best voice changer for PC then you need to try HitPaw. It’s easy to use, affordable and contains one of the most realistic voices on the market.
FAQs
Can I make my voice sound like a girl?
Yes, You can make your voice sound like a girl using a voice changer for PC and online. Some voices are preset by cloning the voices of popular celebrities. While others are AI-generated from training made from many different voices.
What makes a girl’s voice?
A girl’s voice is characterized by higher pitch, smoother intonation, and softer articulation compared to a masculine voice. It often involves speaking with a more melodious tone and using a wider vocal range, reflecting societal perceptions of femininity in speech patterns.
Can a guy fake a girl’s voice?
It’s very easy to fake a girl’s voice as a guy. All you need is a voice changer with a realistic voice. Most of the platforms have a huge library with different girl voices that you can choose from
APPS & SOFTWARE
VMS Video Management Software: Revolutionizing Surveillance

Introduction to vms video management software and its Importance
In a world where security is paramount, the tools we use to safeguard our spaces must evolve. Enter VMS video management software a game changer in the realm of surveillance. As technology advances, so too does our ability to monitor, analyze, and respond to incidents in real-time. The importance of VMS cannot be overstated; it offers not only enhanced situational awareness but also peace of mind for businesses and individuals alike.
Imagine having a centralized platform that streamlines your entire security system. From monitoring live feeds to storing vast amounts of footage securely, VMS provides an efficient solution tailored for modern needs. This software empowers users with robust features that enhance overall safety while simplifying operations. Whether you’re managing a small storefront or overseeing a large facility, understanding the capabilities and advantages offered by VMS can transform how you approach security challenges.
Join us as we delve deeper into the world of VMS video management software and discover why it’s revolutionizing surveillance across various sectors.
Advantages of using VMS for Surveillance
VMS video management software offers a myriad of advantages for modern surveillance systems. First and foremost, it streamlines the monitoring process, allowing users to manage multiple camera feeds from a single interface.
This centralized control enhances situational awareness in real-time. Users can quickly switch between different views and access recorded footage with ease.
Another significant benefit is scalability. Whether you’re managing a small store or an extensive corporate campus, VMS can grow with your needs. Adding new cameras or integrating advanced features becomes seamless.
Additionally, VMS solutions often include sophisticated analytics tools such as (lot). These capabilities enable automated alerts for suspicious behavior or unusual patterns, drastically improving response times.
Enhanced user access controls also set VMS apart. Administrators can customize permissions based on roles within the organization, ensuring that sensitive data remains protected while still being accessible to those who need it most.
Features and Capabilities of VMS
VMS video management software offers a robust suite of features designed to enhance surveillance capabilities. One key feature is real-time monitoring, allowing users to view live feeds from multiple cameras simultaneously. This ensures that critical events are captured as they happen.
Another important capability is advanced analytics. Many VMS solutions incorporate artificial intelligence, enabling facial recognition and motion detection. These tools help identify potential security threats quickly.
User-friendly interfaces make navigation intuitive, even for those new to the technology. In addition, cloud storage options provide scalability and flexibility in managing large volumes of footage without the need for extensive hardware investments.
Integration with other security systems is seamless. Whether connecting alarms or access controls, VMS creates a comprehensive security ecosystem tailored to specific needs. Customizable alerts also keep users informed about unusual activities in real time, ensuring proactive responses when necessary.
Case Studies: Real-life Examples of VMS Implementation
Companies across various sectors have harnessed the power of VMS video management software to enhance their security measures.
For instance, a large retail chain implemented VMS to streamline surveillance in its stores. By integrating multiple cameras into one interface, they reduced theft by 30% within six months. The real-time alerts enabled staff to respond quickly to incidents.
In another case, a university adopted VMS for campus safety. With hundreds of cameras installed, the system allowed security personnel to monitor live feeds from any location. This flexibility led to faster response times during emergencies and improved student safety.
A city government also turned to VMS for public safety monitoring in parks and public areas. This initiative resulted in enhanced crime prevention strategies and increased community trust as residents felt more secure with visible surveillance efforts.
These examples illustrate how versatile and impactful VMS can be across diverse environments.
Future of VMS and its Impact on Security
The future of VMS video management software is bright, especially in the realm of security. As technological advancements continue to unfold, so does its potential to transform surveillance.
Artificial intelligence and machine learning are set to become foundational elements of future strategy. These technologies can analyze footage in real-time, identifying unusual behavior or threats instantly. This capability enhances responsiveness, allowing security teams to act swiftly when needed.
Moreover, cloud integration will revolutionize data storage and accessibility. Remote access means users can monitor feeds from anywhere at any time. This flexibility not only improves convenience but also broadens the scope for proactive security measures.
As cyber threats evolve, robust cybersecurity features within VMS become crucial. Future iterations will likely incorporate advanced encryption methods and user authentication protocols to safeguard sensitive information.
The growing importance of data analytics will also shape VMS development. By offering insightful reports on traffic patterns or incident histories, organizations can make informed decisions that enhance overall safety strategies.
How to Choose the Right VMS for Your Needs?
Selecting the right VMS video management software can feel overwhelming. Begin by evaluating your unique security requirements. Consider the size of your facility and the number of cameras you plan to use.
Next, think about scalability. Choose a system that can grow with your organization. This flexibility is crucial for future expansions or upgrades.
User interface is another key factor. A user-friendly layout will make it easier for your team to navigate through footage and manage settings efficiently.
Don’t forget about integration capabilities as well. Ensure that the VMS can work seamlessly with existing hardware and other security systems, such as alarms or access control.
Evaluate customer support options offered by vendors. Dependable support guarantees immediate assistance during crises, keeping critical system downtime to an absolute minimum.
Conclusion
The rise of VMS video management software marks a significant shift in how surveillance is approached. Its importance lies not only in enhancing security but also in streamlining operations and improving overall efficiency. The advantages it offers, such as scalability, ease of use, and real-time monitoring capabilities, are compelling reasons for businesses to adopt this technology.
With features that include advanced analytics and cloud integration, VMS provides users with tools to optimize their security systems. Real-life implementations showcase its effectiveness across various sectors, demonstrating just how transformative this software can be.
Looking ahead, the future of VMS appears bright. As technology continues to advance, we can expect even more sophisticated applications that will further enhance safety protocols across industries.
Choosing the right VMS for your needs involves assessing specific requirements including budget constraints and desired functionalities. By doing thorough research and considering expert recommendations, organizations can select a system that aligns perfectly with their objectives.
As the landscape of surveillance evolves through innovations like VMS video management software, embracing these changes becomes imperative for anyone serious about security today.
APPS & SOFTWARE
Winux Password: Complete Guide to Setup, Reset & Security
What Users Actually Want to Know About Winux Password
People searching “winux password” fall into three clear groups. The first group just got access to a Winux system. They need to know the winux default password and how to change it fast. The second group is locked out. They need winux password recovery steps that actually work. The third group manages teams or servers. They care about winux password policy, compliance, and long-term winux account security.
This guide covers all three. No fluff. No wasted time. Understanding user intent matters here because Winux sits in a unique space. It combines the familiar feel of Windows with the raw power of a Linux kernel. That hybrid nature means its winux authentication system behaves differently from both. You need to know those differences before you touch anything.
Whether you’re a home user or an IT admin managing a winux multi-user environment, the rules below apply to you. Follow them in order. Skip nothing.
How the Winux Authentication Architecture Actually Works?
Winux does not handle passwords the way Windows does. It uses PAM (Pluggable Authentication Modules) at its core. PAM is a battle-tested Linux framework. It controls every login attempt, session check, and password change request on the system.
When you type your password, PAM intercepts it. It checks the hash stored in the system’s shadow file. If the hashes match, you get in. If not, access is denied. Simple on the surface. Complex underneath.
The winux password hash format is SHA-512 by default. This is one of the strongest hashing algorithms available for credential storage today. It aligns with NIST SP 800-63B recommendations for digital identity assurance. Most consumer operating systems still use weaker methods. Winux does not cut corners here.
The sudoers file controls who can escalate privileges. This is critical in any winux user management setup. Only trusted users should have sudo rights. The wrong configuration here opens massive security holes. Every admin needs to audit this file before deploying Winux in a production environment.
| Feature | Winux | Standard Linux | Windows 11 |
|---|---|---|---|
| Password Hashing | SHA-512 | SHA-512 / MD5 | NTLM / Kerberos |
| Auth Framework | PAM | PAM | LSASS |
| 2FA Support | Native | Plugin-based | Azure AD required |
| Password Policy Engine | Built-in | Manual config | Group Policy |
| Recovery Mode | Boot-level | Boot-level | WinRE |
| Default Password Expiry | 90 days | None | 42 days |
Setting Your Winux Password for the First Time
First boot is your most important security moment. The winux default password is set during installation. It is almost always something generic. Change it immediately. No exceptions.
Open the terminal. Type passwd and press Enter. You will be prompted for your current password, then your new one twice. Use a minimum of 12 characters. Mix uppercase, lowercase, numbers, and symbols. This is not optional — it is the baseline standard under winux password strength guidelines.
If you are setting up a new user account, use sudo adduser username first. Then assign a password with sudo passwd username. The winux credential management system stores this immediately in encrypted form. You will never see the raw password stored anywhere in plain text.
For system administrators managing a winux multi-user environment, enforce password rules at the policy level. Edit /etc/pam.d/common-password to set minimum length, complexity, and reuse restrictions. This single file governs winux password policy for every account on the system. Get it right from day one.
Winux Password Reset: Step-by-Step Recovery
Getting locked out happens. The winux password reset process depends on one thing: do you still have root access or not?
If you have root access: Log in as root or use another sudo-enabled account. Run sudo passwd targetusername. Enter the new password twice. Done. The locked user can now log in with the new credentials. This is the fastest path and the one most IT teams use during routine winux account security maintenance.
If you have no root access: You need to enter recovery mode. Restart the system. Hold Shift during boot to access the GRUB menu. Select “Advanced options” then “Recovery mode.” From the root shell prompt, mount the filesystem with write permissions using mount -o remount,rw /. Now run passwd username to reset any account. Reboot normally when done.
If the entire system is inaccessible: Boot from a live USB. Mount the Winux partition. Use chroot to enter the system environment. Run the passwd command. This method follows the same logic used in standard Linux winux password recovery procedures. It works even on fully encrypted systems if you have the disk decryption key.
Do not skip the reboot after recovery. Some PAM modules cache authentication data. A fresh boot clears everything and applies your new winux secure login settings properly.
Deep Expert Insights: Hardening Winux Password Security
Security professionals who work with hybrid OS environments know one truth: default settings are never enough. Winux gives you the tools. You have to use them.
Start with winux two-factor authentication. Winux supports Google Authenticator and similar TOTP apps through PAM. Install the libpam-google-authenticator package. Run the setup wizard. Edit /etc/pam.d/sshd to require the second factor. This one change blocks the vast majority of brute-force and credential-stuffing attacks against your system.
Next, address winux password encryption at the storage level. Confirm your shadow file uses $6$ prefix entries — that confirms SHA-512 hashing is active. If you see $1$ entries, those accounts use MD5. That is a critical vulnerability. Force a password reset for those accounts immediately and update your PAM configuration.
Review your winux access control model. Not every user needs login access to the machine. Use usermod -L username to lock accounts that should not have interactive access. Service accounts should never have shell access. Set their shell to /usr/sbin/nologin in /etc/passwd. These two steps alone significantly reduce your attack surface.
Finally, set up automated password expiration. Edit /etc/login.defs and set PASS_MAX_DAYS 90, PASS_MIN_DAYS 7, and PASS_WARN_AGE 14. This enforces regular credential rotation across all accounts. It aligns directly with NIST SP 800-63B recommendations and keeps your winux system security posture audit-ready.
Implementation Roadmap: Winux Password Management in 5 Stages
Stage 1 — Baseline Audit (Day 1) List all user accounts. Identify accounts with no password, weak passwords, or MD5 hashing. Flag service accounts with shell access. This gives you your security debt.
Stage 2 — Policy Configuration (Day 1-2) Edit PAM files and login.defs. Set complexity rules. Set expiration windows. Enable lockout after 5 failed attempts using pam_faillock. Document every change.
Stage 3 — Credential Reset (Day 2-3) Force password resets for all flagged accounts. Use chage -d 0 username to force a reset on next login. Users set their own new passwords. You never see them.
Stage 4 — 2FA Rollout (Day 3-5) Deploy winux two-factor authentication for all admin accounts first. Expand to all users within the same week. Test thoroughly before enforcing system-wide.
Stage 5 — Monitoring & Maintenance (Ongoing) Enable login attempt logging. Review /var/log/auth.log weekly. Set up alerts for repeated failures. Schedule quarterly audits of the winux user management system. Rotate service account credentials every 60 days.
Winux Password Security in 2026: What’s Coming
The password landscape is shifting fast. By 2026, expect winux login credentials to evolve beyond text-based inputs entirely for many use cases.
Passkey support is coming to Winux. The FIDO2 standard, already adopted by major browser vendors, is being integrated into PAM-based systems. This means biometric and hardware-key authentication will work natively in winux secure login flows. No password to remember. No password to steal.
Winux password policy will also shift toward behavioral authentication. Instead of just checking what you know, the system will check how you behave — typing rhythm, login timing patterns, and device fingerprint. This adds a passive second layer without any user friction.
AI-driven anomaly detection will monitor winux credential management systems in real time. Unusual login patterns will trigger automatic lockdowns. Security teams will spend less time on manual log reviews and more time on strategic hardening.
The systems you build today should account for this shift. Use open standards. Avoid vendor lock-in. Keep your winux authentication system modular. PAM’s pluggable design means you can swap in new authentication methods without rebuilding from scratch. That flexibility is Winux’s biggest security advantage heading into 2026.
FAQs
What is the winux default password after installation?
Winux does not ship with a universal default password. During installation, you set the root and primary user passwords manually. Some OEM deployments use “winux” or “admin” as placeholders — change these immediately using the passwd command.
How do I reset my winux password if I’m completely locked out?
Boot into recovery mode via GRUB. Access the root shell. Remount the filesystem with write permissions using mount -o remount,rw /. Then run passwd yourusername to set a new password. Reboot and log in normally.
Is winux password encryption strong enough for enterprise use?
Yes. SHA-512 hashing combined with PAM-based access control meets enterprise security standards. For full compliance with NIST SP 800-63B, add two-factor authentication and enforce password expiration policies through login.defs and PAM configuration.
How do I enforce a winux password policy across multiple users?
Edit /etc/pam.d/common-password to set complexity requirements. Edit /etc/login.defs for expiration rules. Use chage to apply per-user settings. For large deployments, automate this with Ansible or a similar configuration management tool.
Can winux support passwordless login?
Yes. Winux supports SSH key-based authentication, which eliminates passwords for remote access entirely. FIDO2 passkey support is on the roadmap for upcoming releases. For local login, biometric PAM modules are available today for fingerprint-based access.
APPS & SOFTWARE
Mastering apd4u9r: The Definitive Guide to High-Resonance System Architecture

The Invisible Friction: Why You Need apd4u9r Now
Most digital infrastructures suffer from what we call “Silent Decay.” You see it as slow load times or intermittent connection drops. The root cause is often a lack of a structured apd4u9r protocol. Without this specific layer, your network topology becomes fragile. Every time a user interacts with your system, a dozen micro-points of failure threaten the user experience.
If you are seeing high latency, your system is likely struggling with inefficient bandwidth allocation. This isn’t just a technical glitch; it is a loss of authority. In the modern economy, a millisecond delay translates to lost revenue. By deploying apd4u9r, you are not just fixing a bug you are building a fortress for your data.
Real-World Warning: Do not mistake a simple reboot for a long-term solution. Band-aid fixes actually increase protocol overhead over time, leading to a total system crash when you least expect it.
Technical Architecture: Aligning with ISO and IEEE Standards
The apd4u9r framework is built on a modular architecture that prioritizes firmware stability. Unlike legacy systems that rely on linear processing, this methodology utilizes hardware acceleration to bypass traditional bottlenecks. We anchor our technical guidelines in the IEEE 802.3 Ethernet standards and the ISO/IEC 38500 corporate governance of IT. This ensures your deployment is globally compliant and technically sound.
At the core of the system lies a sophisticated error correction engine. This engine doesn’t just find mistakes; it predicts them using heuristic analysis. By implementing a robust jitter buffering strategy, the apd4u9r methodology smooths out the peaks and valleys of data transmission. This results in a “Flatline Stability” profile that is the gold standard for enterprise computing.
The integration of redundancy checks at every layer prevents the “Single Point of Failure” trap. When you build with this level of scalability, your infrastructure can grow from 1,000 to 1,000,000 users without requiring a complete redesign. It is about future-proofing your API handshake protocols today so they don’t break tomorrow.
Features vs. Benefits: The Performance Delta
| Feature | Technical Benefit | Business Impact |
| Throughput Optimization | Maximizes data flow per second. | Faster user experience & lower churn. |
| End-to-end Encryption | Secures data at rest and in transit. | Mitigates legal risk and builds trust. |
| Load Balancing | Distributes traffic across nodes. | Eliminates server downtime during peaks. |
| API Handshake | Seamless third-party connections. | Accelerates legacy integration timelines. |
Pro-Tip: Always prioritize bandwidth allocation for your core transactional data. Never let background updates starve your primary revenue-generating throughput.
Expert Analysis: What the Competitors Aren’t Telling You
Most “experts” will tell you that adding more servers solves performance issues. This is a lie. Scaling horizontally without an apd4u9r strategy just creates a more expensive, broken system. The real secret lies in latency reduction at the software level, not just the hardware level. You need to optimize your packet-loss mitigation logic before you throw money at more RAM or CPU power.
Another overlooked factor is legacy integration. Many modern tools claim to be “plug-and-play,” but they often clash with older Cisco IOS or local firmware versions. The apd4u9r methodology acts as a universal translator. It creates a “buffer zone” where modern edge computing can safely talk to older databases without causing data corruption or protocol overhead.
Finally, watch out for “Security Bloat.” Many security tools add so much latency that they render the system unusable. Our approach uses hardware acceleration for end-to-end encryption, ensuring that your data is safe without slowing down your API handshake.
Step-by-Step Practical Implementation Guide
- Environment Audit: Use Wireshark to capture a 24-hour traffic log. Identify where your current packet-loss is occurring.
- Protocol Selection: Choose the apd4u9r module that matches your industry (e.g., Fintech vs. Healthcare).
- Deploy Monitoring: Set up Prometheus and Grafana to track latency reduction in real-time.
- Hardware Acceleration: Enable specialized processing on your network cards to handle error correction tasks.
- Validation: Run a stress test that mimics 200% of your peak load. Watch for jitter buffering efficiency.
Future Roadmap for 2026 & Beyond
As we move deeper into 2026, the apd4u9r framework will evolve to incorporate AI-driven load balancing. We are looking at a future where network topology is self-healing. If a node fails, the system will automatically reroute traffic based on uptime reliability scores without human intervention.
Edge computing will become the primary host for apd4u9r nodes. By moving the processing power closer to the user, we can achieve near-zero latency. This will be essential for the next generation of decentralized applications and high-fidelity virtual environments.
Visual Advice: Place a Technical Flowchart here showing the "Data Journey" from the Edge Device through the apd4u9r Error Correction engine to the Cloud Database.
FAQs
What is the primary function of apd4u9r?
It is a strategic framework used to optimize data integrity and reduce system friction in high-volume environments.
Is apd4u9r compatible with Kubernetes?
Yes. In fact, using Kubernetes for orchestration is the recommended way to ensure scalability and load balancing.
How does it improve latency?
By reducing protocol overhead and utilizing hardware acceleration, it streamlines the path data takes from sender to receiver.
Do I need new hardware to implement this?
Not necessarily. Most modern servers support the firmware stability updates required to run the core apd4u9r modules.
How does this impact E-E-A-T?
By ensuring uptime reliability and data integrity, you provide a superior user experience, which is a core signal for Expertise and Trustworthiness.

 HOME IMPROVEMENT1 year ago
HOME IMPROVEMENT1 year agoThe Do’s and Don’ts of Renting Rubbish Bins for Your Next Renovation

 BUSINESS1 year ago
BUSINESS1 year agoExploring the Benefits of Commercial Printing

 HOME IMPROVEMENT11 months ago
HOME IMPROVEMENT11 months agoGet Your Grout to Gleam With These Easy-To-Follow Tips

 HEALTH11 months ago
HEALTH11 months agoThe Surprising Benefits of Weight Loss Peptides You Need to Know

 TECHNOLOGY1 year ago
TECHNOLOGY1 year agoDizipal 608: The Tech Revolution Redefined

 HEALTH10 months ago
HEALTH10 months agoYour Guide to Shedding Pounds in the Digital Age

 BUSINESS1 year ago
BUSINESS1 year agoBrand Visibility with Imprint Now and Custom Poly Mailers

 HEALTH1 year ago
HEALTH1 year agoHappy Hippo Kratom Reviews: Read Before You Buy!









