Uncategorized
The Role of Drug Tests in Workplace Safety and Productivity

Safety and productivity depend on drug testing for the workplace. Programs for drug testing help to lower workplace drug risks, increase productivity, and safeguard workers.
Drug testing finds prescription and illegal drugs. Depending on the profession and industry, companies screen for particular substances or classes of drugs using various drug test panels. Different types of drug tests panels might look for drugs including marijuana, cocaine, opioids, amphetamines, and benzodiazepines. Drug testing promotes responsibility, keeps workplace safety, and discouragement of drug use.
As they put in place drug testing programs incluiding saliva drug test kit, companies have to handle ethical and legal questions. Rules and policies must be followed to protect employee privacy and a safe, drug-free workplace. Setting explicit policies, providing education and support, and fairly and regularly running drug tests help employers to reconcile employee rights with workplace safety.
Different types of drug tests panels ensure safety and compliance in workplaces, athletic events, and rehabilitation programs. These panels use many assays to detect illegal drugs and prescription drug abuse. Urine, hair follicle, saliva, and blood tests are common drug testing. Each test has different detection window, accuracy, and convenience advantages and disadvantages. Organizations and individuals must understand drug testing, how they function, and why they matter to make informed drug screening decisions. Drug testing panels help companies create a secure, drug-free workplace and help employees comply and recover.
Types of Drug Tests
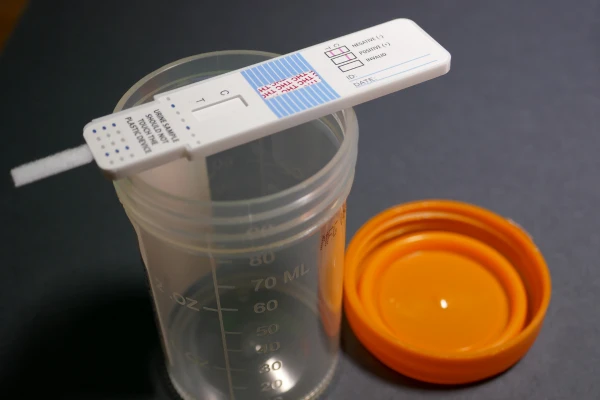
Urine Drug Testing
One often used types of drug tests panels is urine drug testing. Drug and metabolite testing of urine samples Opiates, cocaine, marijuana, amphetamines, benzodiazepines, and more may all be found by urine drug testing. These tests make use of drug test panels—which identify particular drug classes or combinations.
Though it is cheap and non-invasive, urine drug testing has certain disadvantages. Widely available and able to expose recent drug usage is urine drug testing One also has to take into account cons. Comparatively to hair or blood tests, urine drug testing have a smaller detecting window. Urine samples could also generate false positives or negatives and compromise privacy issues.
Notwithstanding its restrictions, urine drug testing is valuable for forensic investigations, drug rehabilitation, and occupational drug testing. The demands of the testing program decide the types of drug tests panels employed, which target particular drugs depending on their design. One should weigh the benefits and drawbacks of urine drug testing in order to guarantee correct findings and make wise judgments.
Saliva (Oral Fluid) Drug Testing
A non-invasive and one of the easiest types of drug tests panels is oral fluid drug testing, sometimes known as saliva drug testing. Over the test, a collector will swab or sponge the patient between their face and gums for a few minutes. Next will be laboratory study of the saliva sample.
Saliva drug tests can find prescribed and illicit narcotics. Commonly discovered drugs in saliva tests are marijuana (THC).
Amphetamines with Cocaine
Opioids:
benzodiazepines
Drug methamphetamine
Pcs
Alcohol (often)
These tests with precision and dependability identify recent drug use inside a specified detecting window. The different types of drug tests panels of the checking facility determine the different components found in saliva tests.
One should weigh benefits and drawbacks of saliva drug testing. For the collectors as well as the test subjects, the non-invasive character of the test makes it practical and comfortable. With real-time results, recent drug use is easily observable.
Another advantage of saliva tests is their ability to identify prescription and illegal medications. This exhaustive coverage aids in the identification of numerous drug usage within a detection range. Saliva drug testing is reliable and accurate when done by a reputable facility using the correct types of drug tests panels.
Saliva drug tests are more accurate in identifying current drug use than in long-term use. Unlike other kinds of drug test panels, such as urine or hair tests, saliva tests have a shorter detection window. Substance and personal qualities define the detection window. Though maybe less sensitive than other drug testing, saliva tests are quite accurate.
Blood Drug Testing
One absolutely effective approach to find drugs is blood drug testing. This drug test retrieves a blood sample from the arm vein. The sample is next checked in a lab for drugs and metabolites.
Different types of drug tests panels vary in composition for blood drug testing. Common are tests for cocaine, marijuana, opioids, amphetamines, and benzodiazepines. Blood drug testing find illegal drugs as well as prescription medications, sedatives, and stimulants.
Accurate, consistent results and a whole picture of a person’s drug use come from blood drug testing. Blood tests’ capacity to identify recent drug use helps occupational safety monitoring and accident investigations.
Blood drug testing has flaws, though. More intrusive and time-consuming than standard drug testing, the collecting technique calls for a trained specialist. Some substances fast metabolize and are undetectable, hence blood drug testing could have a smaller detection window than urine or hair tests.
Blood drug testing finds application in workplace drug testing programs, forensic investigations, and healthcare despite these obstacles. It provides a whole picture of someone’s drug intake, therefore guaranteeing their safety and well-being.
Breath Alcohol Testing
Measuring alcohol levels is done mostly by breath alcohol tests. Breathalyzers evaluate alcohol levels by means of breath samples. For quick, accurate testing—urgent—this non-invasive, fast, exact alcohol testing is excellent.
Breath alcohol testing is best in critical situations such police roadside sobriety checks, occupational safety guidelines, and post-accident investigations. It enables on-site testing, therefore enabling authorities to rapidly identify drunk drivers.
Breath alcohol testing has several advantages in companies where staff safety is of great importance. It guarantees worker safety by simplifying and effective alcohol impairment detection. Breath alcohol testing’s non-invasive character helps to lower employee privacy concerns and discomfort. By routinely testing, companies can keep employees productive and avoid alcohol-related incidents.
Note that breath alcohol testing looks for alcohol only—not medications. Drug testing makes use of urine, blood, hair, and saliva drug test panels—each with advantages and uses.
Factors to Consider When Choosing a Drug Test
Drug testing standards vary by industry, and the work environment may affect the type of drug test panels needed. Transportation and construction industries may need more thorough drug test panels to protect workers and the public. However, less safety-sensitive businesses may choose smaller drug test panels.
Different types of drug tests panels cost more. For the best drug testing program, examine your organization’s budget and allocate resources. Test frequency should also be considered. Testing may be required by some organizations more often than others. Understanding budget limits and testing frequency will help choose drug test panels that balance accuracy, affordability, and industry regulations.
Industry norms should guide drug test panel selection. To choose the right drug test panels, you must analyze your workplace and its dangers. Organizations should emphasize employee safety, avoid legal risks, and maintain a productive, drug-free workplace by considering these criteria.
Testing the dependability of multiple types of drug tests panels can help organizations choose the most accurate testing procedures. Based on detection windows, sensitivity, and adulteration possibility, urine, saliva, hair, and blood tests have varied levels of accuracy. Urine tests are most prevalent and provide a wide detection window, whereas saliva tests are convenient and shorter. Hair tests detect more but are less adulterable. Blood tests are accurate but usually used for post-accident testing.
Choosing the Best Testing Method and Panel for Your Needs
Drug testing programs help companies detect and prevent substance usage, which can affect job performance, safety, and productivity. When customizing the types of drug tests panels for your company, consider industry standards and regulatory constraints. This includes choosing the right drug test panels for your company and aligning them with industry standards. Customizing the drug testing plan to your organization’s needs can develop a thorough and effective strategy that fosters a safer and healthier workplace.
Different drug test panels target different groups of drugs. The panels you choose rely on your industry, legal regulations, and the contaminants that threaten your company. Urine, hair, saliva, and blood drug test panels have pros and cons. To choose the right panel(s) for your business, consult experts and consider industry standards and recommendations. You may create a comprehensive drug testing program that improves workplace safety and productivity by choosing the finest types of drug tests panels and matching it to your organization’s needs.
Uncategorized
Anonib AZN: Examining Privacy Risks and Niche Forum Culture

Introduction to Anonib AZN and its origins
In the ever-evolving landscape of online forums, Anonib AZN has carved out a niche that’s as intriguing as it is controversial. Born from the need for anonymity and open dialogue, this platform offers users a unique space to engage with others who share similar interests or experiences. But what lies beneath its surface? With vibrant discussions often mingling with darker themes, Anonib AZN presents both opportunities and challenges in equal measure. Dive into this exploration of privacy risks and community dynamics as we unravel the complexities surrounding one of the internet’s most talked-about platforms.
The Controversial Nature of Anonib AZN
Anonib AZN has garnered a reputation for being at the center of controversy. As an anonymous forum, it thrives on users sharing personal and sometimes sensitive content. This anonymity breeds both freedom and recklessness.
Users often engage in discussions that can be provocative or offensive. Topics range from relationships to explicit adult content, leading to heated debates about morality and ethics. What one person finds humorous, another might deem inappropriate.
The lack of accountability allows individuals to express themselves without fear of repercussions. However, this also raises questions about responsible discourse online.
Critics point out that such environments can encourage harmful behavior or harassment under the cloak of anonymity. The blurred line between free speech and harmful content continues to fuel discussions surrounding Anonib AZN’s role in online communities.
Privacy Risks on Anonib AZN
Anonib AZN operates under a veil of anonymity, but this facade hides significant privacy risks. Users often share sensitive information that can be easily exposed or misused.
Due to the lack of moderation, malicious actors thrive on the platform. They may exploit personal data for harassment or identity theft. The anonymous nature emboldens some users to engage in unethical behavior without accountability.
Moreover, even though posts appear transient, they often leave digital footprints. Captured images and distributed URLs often cause content to persist significantly longer than originally anticipated. Once something is online, controlling its spread becomes nearly impossible.
Users should remain vigilant about what they choose to disclose. Understanding these risks is crucial for anyone engaging with Anonib AZN’s community dynamics and sharing culture.
Niche Forum Culture on Anonib AZN
Anonib AZN thrives on a unique form of niche forum culture. This space attracts individuals seeking anonymity and shared interests, often surrounding sensitive topics.
Members communicate through threads that can range from personal experiences to societal discussions. The atmosphere is casual yet charged, allowing users to express themselves without fear of repercussions. This fosters a sense of community among participants who share similar backgrounds or life experiences.
The subcultures within Anonib AZN are diverse, leading to vibrant discussions. Users find solace in the relatability of others’ stories and opinions. However, this environment also enables fringe ideas to circulate more freely.
Despite the potential for toxicity, many find value in this unfiltered exchange of thoughts. It serves as an outlet for those feeling marginalized elsewhere online or offline. Each post contributes to an ongoing narrative that shapes the experience on the platform daily.
The Impact of Anonib AZN on Society
Anonib AZN has carved out a distinct niche in the vast landscape of online forums. This platform serves as a digital haven for those seeking anonymity, allowing users to share thoughts without fear of judgment.
The forum fosters candid discussions around various topics, from personal experiences to controversial viewpoints. It creates an environment where individuals feel liberated to express themselves openly.
However, this freedom comes with consequences. The ability to post anonymously can lead to toxic behavior and misinformation spreading rapidly. Users may say things they wouldn’t dare express face-to-face.
Moreover, Anonib AZN plays a role in shaping subcultures. Groups form based on shared interests or struggles, leading to both camaraderie and division within society at large.
As it continues evolving, its influence will likely spark conversations about ethics and responsibility in anonymous spaces. Society must weigh the benefits against the potential societal pitfalls that accompany such platforms.
Alternatives to Anonib AZN for Anonymous Sharing
For those seeking alternatives to Anonib AZN, several platforms cater to anonymous sharing without compromising privacy. Reddit offers various subreddits where users can discuss intimate topics anonymously while engaging with a vast community.
Another option is 4chan, known for its ephemeral threads and diverse user base. It allows individuals to post freely, although it comes with its own set of risks regarding content moderation.
If you’re looking for something more structured, consider using platforms like Whisper or Yik Yak. These apps focus on anonymous messaging and local sharing, encouraging open discussions about personal experiences in a safer environment.
Consider encrypted messaging apps such as Signal or Telegram’s secret chats. While not forums per se, they provide anonymity through end-to-end encryption and are great for private conversations without the fear of exposure.
Conclusion: The Future of Anonib AZN and Online Forums
The future of Anonib AZN and similar online forums remains uncertain. As digital landscapes evolve, the need for privacy is more pressing than ever. Users are becoming increasingly aware of their data rights and the risks associated with sharing personal information online.
While Anonib AZN has carved out a niche for itself, it also faces scrutiny from both users and authorities who question its impact on community standards and safety. The delicate balance between anonymity and accountability will likely shape its trajectory.
Emerging platforms may adopt lessons learned from Anonib AZN’s journey, prioritizing user security while fostering healthy discussions in niche circles. It’s crucial for these new spaces to prioritize transparency without compromising the essence of anonymous interactions that many users cherish.
As technology continues to advance, so will the methods used by individuals seeking safe havens for expression whether through revamped versions of existing forums or entirely new concepts altogether. The conversation around privacy, culture, and engagement is ongoing; how this unfolds could redefine our understanding of community in digital realms moving forward.
Uncategorized
Bonus Pokies Australia Guide
Top Online Casinos for Bonus Pokies Australia
- BTC & ETH
- TOP ODDS
- VIP BONUS
- INSTANT PLAY
- LIVE CASINO
- FAST CASHOUT
- QUICK SIGNUP
- BIG JACKPOT
- SECURE PAY
- QUICK SIGNUP
- TOP ODDS
- VIP BONUS
- LIVE CASINO
- NO KYC
- SECURE PAY
- ODDS BOOSTS
Popular Gaming Services with Bonus Pokies Australia
Licensed online casinos in Australia deliver more than just slot games. Bonus pokies australia platforms give access to secure poker, live roulette, card games, instant lottery titles and progressive jackpot pokies. Each service adds variety and value for all players.
Top-rated online slots on bonus pokies australia
Online pokies are digital versions of classic slot machines you’d find in land-based venues. With dynamic themes, interactive bonuses and auto-spin, modern online pokies offer entertainment and reward potential. Below, explore the leading Australian pokies online and find your favourite instantly.
- Top Online Casinos for Bonus Pokies Australia
- Popular Gaming Services with Bonus Pokies Australia
- Best Online Pokies – Bonus & Features
- Types of Bonus Pokies Promotions
- Who Should Use Pokies Bonuses?
- How Bonus Pokies Australia Offers Work
- Wagering Requirements & Key Conditions
- Common Mistakes To Avoid
- Safe Gambling Tips in Australia
- Payment Methods for Pokies Bonuses
- How to Tell If Online Casinos Are Legit
- FAQ on Bonus Pokies Australia
Top Online Casinos for Bonus Pokies Australia
Australian players often look for trusted operators offering exclusive free spins and no-deposit bonuses for pokies. Here is a list of well-known platforms providing diverse pokies bonuses:
- Royal Reels Casino
- King Johnnie Casino
- PlayAmo Casino
- Fair Go Casino
- Ozwin Casino
- Woo Casino
Popular Gaming Services with Bonus Pokies Australia
Beyond pokies, most Australian casinos offer:
- Classic Online Pokies
- Poker
- Blackjack
- Live Roulette
- Baccarat
- Scratch Cards
- Keno
- Live Dealer Games
Best Online Pokies – Bonus & Features
Choose from hundreds of popular pokies in Australia, often with unique bonus features:
- Lightning Link
- Big Red
- Queen of the Nile
- Buffalo King
- Wolf Gold
- Starburst
- Gonzo’s Quest
- Fruit Party
Types of Bonus Pokies Promotions
There are several variants of bonus pokies australia promotions. They include:
- Welcome Bonuses: For new sign-ups.
- No Deposit Bonuses: Claimed without any deposit.
- Free Spins: Given for popular pokies launches.
- Reload Bonuses: Offered to returning players.
- Loyalty Rewards: Earned through VIP programs.
Who Should Use Pokies Bonuses?
Bonus pokies australia options suit both new and seasoned Australian players. Newcomers get a risk-free start. Experienced players get more spins or cash returns. Make sure you check eligibility by age and residency and always read local regulations.
How Bonus Pokies Australia Offers Work
These bonuses come in various formats. You may need to input a promo code or just opt in during registration. After claiming, the spins or funds are credited to your account. Most platforms have an easy step-by-step claiming process. Playthrough requirements apply before withdrawal.
Wagering Requirements & Key Conditions
Key conditions for bonus pokies australia promotions:
- Wagering: How many times you must bet bonus funds.
- Eligible Games: Only selected pokies may qualify.
- Time Limits: Use within given period or forfeit bonus.
- Max Winnings: Caps on how much you can win or withdraw.
- Payment Restrictions: Not all deposit methods may qualify.
Common Mistakes To Avoid
Players often lose out due to overlooked terms. Here are mistakes to avoid:
- Failing to read wagering requirements.
- Claiming bonuses without checking game eligibility.
- Not using bonus within expiry period.
- Assuming all deposit methods are valid for the offer.
- Not verifying casino licensing.
- Playing with more than one account.
- Requesting withdrawal before completing wagering.
Safe Gambling Tips in Australia
Stick to your budget and remember gambling is for entertainment. Use in-built casino tools to set limits or take breaks. It’s important to avoid chasing losses. If you ever feel out of control, seek help early through local resources or support hotlines.
Payment Methods for Pokies Bonuses
| Payment | Type | Processing Time |
|---|---|---|
| Visa/Mastercard | Credit/Debit | Instant |
| Neosurf | Prepaid | Instant |
| Bitcoin | Cryptocurrency | 1-2 Hours |
| Bank Transfer | Banking | 2-5 Days |
| POLi | Online Bank | Instant |
How to Tell If Online Casinos Are Legit
Only play at licensed platforms. Check for independent auditing and fair-play seals. Read reviews from real players and confirm encryption. Stay away from sites with poor transparency or unclear terms and conditions. The safest casinos also provide responsible gambling support.
FAQ on Bonus Pokies Australia
What is the best bonus for pokies in Australia?
Look for high free spin counts and reasonable wagering under fair terms.
Can I get a bonus without a deposit?
Yes, some online casinos in Australia offer no deposit pokies bonuses for new players.
Are bonus pokies Australia offers available to everyone?
Most are for new sign-ups from Australia, but check age and residency rules carefully.
How do I clear my bonus winnings?
Meet the wagering requirements, then your balance becomes withdrawable as cash.
Are pokies bonuses safe to claim?
Yes, if you stick to licensed and regulated Australian online casinos with clear T&Cs.
Where to Get Help with Gambling Addiction in Australia
If you’re struggling with control over your pokies play, consider speaking to Gambling Help Online or call a confidential hotline. Australian support services can help you set safe limits or take a break from gambling entirely.
Nova Jackpot in Australia
Nova Jackpot stands out among online casinos in Australia thanks to its fresh game line-up and user-friendly platform. With a selection of popular pokies, table games, and live dealer experiences, players are drawn in by frequent promotions and reliable payout systems. Nova Jackpot covers a wide range of payment solutions, including crypto, ensuring smooth transactions for locals.
Slotexo Gaming Options
Slotexo is all about vibrant slots with quality graphics. Its portfolio includes both classic reels and innovative video slots, regularly updated by top providers. Slotexo’s mobile site ensures a high-quality experience on Android and iOS, making it a go-to for Australian pokie fans on the move.
Free Spinz for Pokie Enthusiasts
Free Spinz delivers on its promise by offering new and active players spins at no cost. A perfect introduction to online pokie gaming or a risk-free thrill for regulars, Free Spinz also features cashback deals and a straightforward sign-up.
The Dog House for Aussie Animal Lovers
The Dog House is a favourite slot title among Aussies, famous for its playful graphics, sticky wilds and rewarding features. While not a standalone casino, you’ll find it at leading brands including Free Spinz and Slotexo. Ideal if you seek lighthearted themes mixed with the chance for massive wins.
Ballys New Wave in Australia
Ballys recently expanded its digital reach, bringing its global credibility to Australian screens. Renowned for robust customer care and a serious loyalty program, Ballys’ site features slots, table games and jackpots powered by leading software.
BitStarz Crypto Potential
BitStarz is a clear frontrunner for Aussies who like to play with Bitcoin or Ethereum. BitStarz holds a global reputation for rapid withdrawals, provably fair games and a rich selection that covers pokies, live games and more.
Black Lotus Features
Black Lotus accepts Australian players looking for unique slots and bonus-driven loyalty schemes. Besides pokies, table games and tournaments spice up the offer. The platform’s regular slot races are a big draw.
CasinoChan for Live Action
CasinoChan boasts an extensive live dealer suite in addition to high-volatility pokies from major studios. For Australians seeking variety, CasinoChan offers quick registration, secure payments and some of the best tournament action around.
Casoola Vibes Down Under
Casoola makes online gaming energetic and engaging with quirky robots and colourful UX. Their bonuses are tailored to newcomers and loyal users, while round-the-clock support ensures smooth navigation. Pokies, jackpots and instant win games all feature.
FortuneJack for Crypto Play
FortuneJack targets cryptocurrency players in Australia, boasting top-rated provably fair slots, live dealer tables and no-hassle withdrawals. Its regular jackpots and vibrant community forums add to the appeal.
Guts Casino Reputation
Guts has a solid footprint in the Australian iGaming scene, especially for sports betting and casino integration. The seamless wallet experience means easy game switching, while the site’s responsible gaming focus is praised by Aussie users.
HellSpin Fast-Growing Choice
HellSpin is one of the newer brands but its Aussie presence is growing fast, thanks to hundreds of pokie games, weekly promotions and seamless mobile optimisation. Players enjoy intuitive navigation and strong customer support.
Jackpot City for Big Wins
Jackpot City is a long-standing contender in the Australian market with a stellar record for mega jackpots and monthly cash draws. Their slots are known for progressive prizes and entertainment value.
N1Bet and Sports Integration
N1Bet suits sports fans who also play pokies. Aussies love the site for its high odds and flawless in-game betting options alongside a robust casino lobby packed with new slot releases.
Planet7Casino Safe Play
Planet7Casino is tailored for a smooth Australian experience, with strong safety controls and a focus on responsible gambling. Regular bonuses and free chip codes are standard.
Poker Star for Card Aficionados
Poker Star brings world-class tournament play to Australian poker fans. Whether cash games or tournaments, the site features specialty zones for beginners and advanced players with transparent prize pools.
Royal Vegas Experience
Royal Vegas delivers a premium casino vibe with luxury theming and a vast range of pokies, blackjack, and roulette. The VIP rewards program is highly rated among serious players across Australia.
Slotastic Game Selection
Slotastic is all about slots fun, especially for mobile play. Australian players gain access to a rotating collection of new slots, instant bonuses and fast payouts in AUD.
Slots Capital for Pokies Lovers
Slots Capital maintains hundreds of pokie titles for different tastes and bankrolls. Its fast registration and broad bonus range make it a solid pick for both low-stakes and high-roller Aussies.
Sportingbet for Sports and Casino
Sportingbet is a seasoned operator for Australian sports betting but also features a competitive casino lobby filled with the latest pokies and card games. A single wallet lets you switch seamlessly between sports and slots.
WildCardCity Energetic Gaming
WildCardCity entertains with its Vegas-style looks and a huge game collection sourced from leading providers. Locals love the regular tournaments, interactive prizes and strong VIP incentives.
Responsible Gambling Notice
For all Australian players, gambling should remain a form of entertainment. Set time and spending limits, play within your means and always choose reputable licensed sites for your safety.
Uncategorized
Wolf Treasures Slot – Quick‑Hit, High‑Intensity Gameplay for the Modern Player
Wolf Treasures is a fresh addition to the casino landscape, landing on the market on January 9, 2025 by Onlyplay. The title immediately draws in fans of wildlife themes and big‑payback excitement thanks to its roaring graphics and a promise of up to ten thousand times the stake.
For players who crave rapid results, Wolf Treasures delivers a short‑burst experience that keeps the adrenaline flowing from one spin to the next.
1️⃣ The Grid That Keeps You Guessing
At its core, the slot is a classic 5‑reel, 3‑row layout that offers 243 ways to win. You’re looking for matching symbols from left to right across adjacent reels – no diagonals, no wild combos beyond the standard substitute.
- Five reels provide enough room for variety without overwhelming the eye.
- Three rows keep the pace swift; each spin completes in under a second.
- Because every spin is independent, you can focus on the next instant without dwelling on past outcomes.
The fast‑turnaround is perfect for players who want to try their luck in a handful of spins before stepping away.
Why Speed Matters
When you’re in a short session, you’re less likely to feel the drag of a long game loop. The quick spin times mean you get more chances to hit that coveted bonus trigger before the clock runs out.
2️⃣ Symbols That Speak Volatility
The game’s symbols are straightforward: four animals – Wolf, Bear, Fox, and an extra Wolf symbol that acts as a special trigger – plus colored gems ranging from Blue and Green to Orange and Purple.
- Animal symbols pay up to 2× your stake for five of a kind.
- Gems offer modest returns – Blue and Green at 1×, Orange and Purple at 1.2×.
- The Wolf symbol also serves as a key to the Jackpot Bonus Game.
A high volatility slot means those big payouts are infrequent but memorable, especially when you’re playing for short bursts.
The Feeling of a Wild Spin
Seeing a Wolf pop up on three consecutive reels can be thrilling; it’s a flash of potential that keeps your heart racing between spins.
3️⃣ Free Spins – The Quick‑Fire Feature
Triggering the Free Spins comes from landing five or more Gold Coin Bonus symbols anywhere on the grid. The first activation hands you five free spins plus a pot that accumulates the values of those bonus symbols.
- Each new bonus symbol during the spins adds to the pot.
- When another set of five bonus symbols lands, you get five more spins and the pot grows.
- The pot pays out in its entirety when a bonus symbol lands.
This mechanic rewards players who hit quick streaks of bonus symbols – precisely what short‑session players enjoy.
Why It Works for Rapid Play
The Free Spins round is self‑contained; you can start it, finish it, and move on without lingering on base‑game mechanics.
4️⃣ Jackpot Bonus Game – Miniature Luck
The Jackpot Bonus Game activates when you fill three or more reels with the Wolf symbol. A single‑reel mini‑slot then spins once, awarding one of four fixed jackpots: Mini (10×), Minor (25×), Major (100×), or Grand (1,000×).
- All jackpots are instant; there’s no further spinning.
- The Grand jackpot is a rare event but delivers instant gratification.
- Because it triggers only when you hit three wolves, it aligns with high‑intensity bursts.
For players who want a single spin to carry massive potential, this feature fits right into a quick session plan.
Managing Expectations
The chances are slim, but the payoff is undeniable – perfect for those who love the adrenaline rush of a single big win.
5️⃣ Buy Bonus – Direct Entry for the Pulse‑Pumper
An optional purchase lets you skip straight into either the Free Spins or the Jackpot Bonus Game by paying eighty times your stake (80x). It’s expensive but offers instant access to high‑payback moments.
- If you’re comfortable with risk, buying the bonus can shorten your session dramatically.
- Players might use this when they’re feeling lucky after a short streak of wins.
- The cost can be justified if you’re eyeing that Grand jackpot or a massive free‑spin pot.
This option aligns with short, high‑intensity play because it eliminates waiting time for triggers.
When to Skip the Wait?
If you’re in a tight window and want to test your luck immediately, buying in can be a worthwhile gamble.
6️⃣ Volatility & RTP – Numbers Behind the Thrill
The slot’s RTP sits at 96.60%, which sits comfortably within industry norms for high‑volatility titles. This figure reflects how much of your total stake will return over time; however, with high volatility you’ll experience long dry spells punctuated by big wins.
- RTP is a long‑term metric; it doesn’t dictate what happens on each spin.
- High volatility means fewer wins but potential for larger payouts.
- Short sessions emphasize those rare big moments rather than steady accumulation.
Understanding these numbers lets you plan your short session around risk tolerance and desired excitement level.
The Balance of Risk & Reward
A player who enjoys quick bursts will likely accept occasional losses in exchange for the chance at a massive payout within minutes.
7️⃣ Session Strategy for Short High‑Intensity Play
A typical session might last five minutes or less – enough time for ten to fifteen spins while still feeling fresh and engaged. Here’s how you can structure it:
- Set a small bankroll: Limit yourself to €5–€10 for one session to avoid chasing losses.
- Start low: Bet €0.10–€0.20 per spin; this keeps your risk small while still giving access to bonuses.
- Watch for triggers: When you hit five Gold Coins or three Wolves quickly, decide whether to play through or grab a free spin before stepping away.
- Use Buy Bonus sparingly: Only if you feel lucky and have room in your budget – it can turn a short session into an instant jackpot chase.
- Exit early: Even if you hit a big win early, consider stopping – you’ve achieved your goal for that burst of excitement.
This approach keeps energy high while preventing burnout from extended play.
Typical Decision Flow
You spin – if you hit a bonus symbol, you take it; if not, you keep spinning until time runs out or your bankroll hits your limit.
8️⃣ Real‑World Example: A One‑Minute Sprint
Picture yourself stepping away from work after lunch; you load Wolf Treasures on your phone, set a €5 budget, and begin spinning:
- Spin 1–5: You hit three Wolves; the Jackpot Bonus Game triggers. You land Minor (25×) and win €125 instantly.
- Spin 6–9: No bonus symbols appear; you keep spinning at €0.10 each.
- Spin 10: Five Gold Coins land; Free Spins activate with a pot of €5.
- Free Spins: Two spins hit bonus symbols that add to the pot; you leave with €15 net earnings after five spins total.
You finish the session with a clear win and a sense that the game delivered its promise of rapid action within minutes.
The Aftermath
You log off with your phone still buzzing slightly from that adrenaline spike – just enough excitement without lingering fatigue.
9️⃣ Responsible Play in Short Sessions
Even though sessions are brief, it’s essential to keep control:
- Set time limits: Use phone timers if needed – don’t let yourself fall into endless spinning loops.
- Avoid chasing losses: If you lose your €5 budget quickly, stop instead of raising stakes to recover lost funds.
- Treat losses as entertainment costs: Remember that every spin is an investment in fun rather than profit pursuit.
This mindset preserves the thrill without turning play into a source of stress or disappointment.
Why Short Sessions Help
The brevity ensures you’re less likely to overplay or become emotionally invested in streaks that could last hours if you were playing longer.
ACTION CALL: Dive Into Wolf Treasures Today!
If you’re after quick thrills and instant payoff potential without committing hours of gameplay, give Wolf Treasures a try. Set your budget, hit spin, and let the wolves lead you toward your next big win in just minutes!

 HOME IMPROVEMENT1 year ago
HOME IMPROVEMENT1 year agoThe Do’s and Don’ts of Renting Rubbish Bins for Your Next Renovation

 BUSINESS1 year ago
BUSINESS1 year agoExploring the Benefits of Commercial Printing

 HOME IMPROVEMENT11 months ago
HOME IMPROVEMENT11 months agoGet Your Grout to Gleam With These Easy-To-Follow Tips

 HEALTH11 months ago
HEALTH11 months agoThe Surprising Benefits of Weight Loss Peptides You Need to Know

 TECHNOLOGY1 year ago
TECHNOLOGY1 year agoDizipal 608: The Tech Revolution Redefined

 HEALTH10 months ago
HEALTH10 months agoYour Guide to Shedding Pounds in the Digital Age

 BUSINESS1 year ago
BUSINESS1 year agoBrand Visibility with Imprint Now and Custom Poly Mailers

 HEALTH1 year ago
HEALTH1 year agoHappy Hippo Kratom Reviews: Read Before You Buy!









