TECHNOLOGY
What is Qt and How Can I Use It?

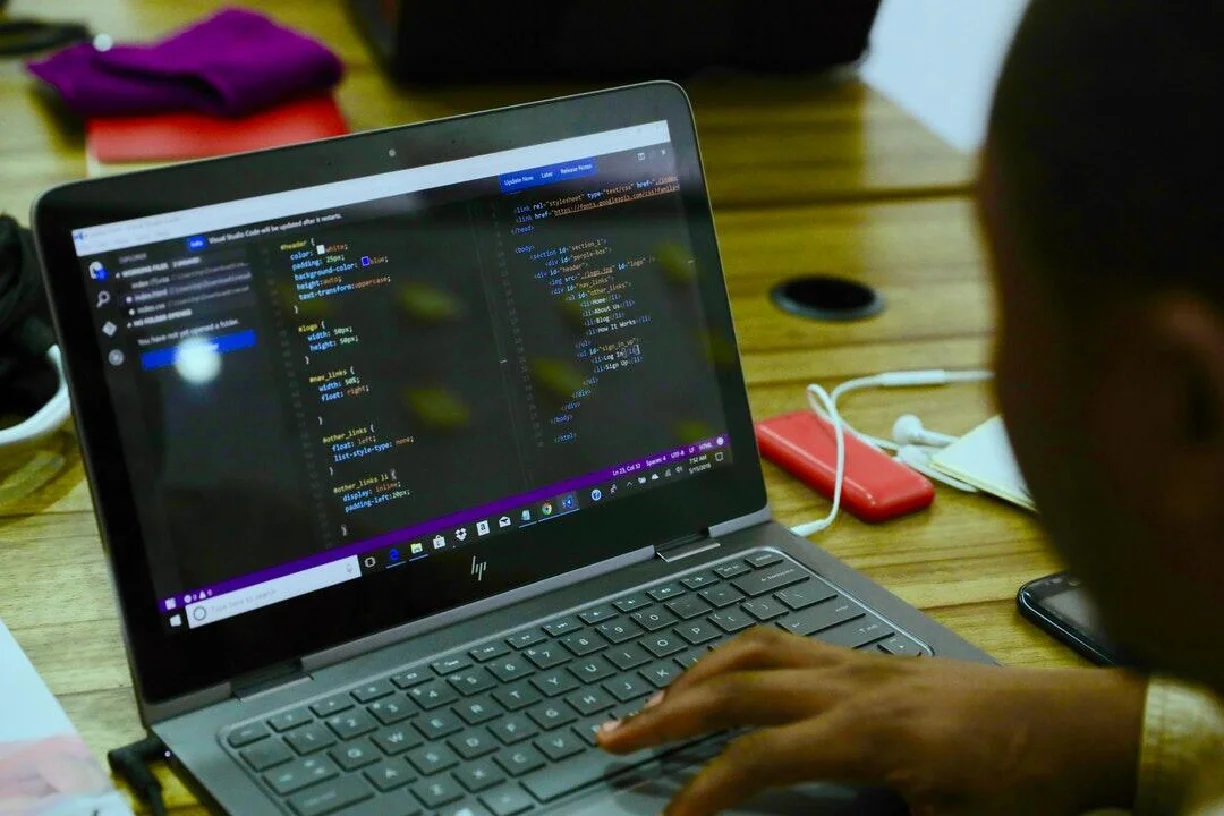
When it comes to software development, the right choice of the framework a developer makes can mean power or even or by how much more easily the program can be moved from one platform to another, cross-platform capabilities, and the user convenience. One such tool so flexible and strong is Qt. But how do you make the most of Qt framework and what exactly is it and how to leverage it for your development projects?
What is Qt?
Qt is a widget taken with the source code and an open-source tool, which is delivering graphical user one itself and a mobile system that exists on various software-on-software platforms as well as hardware platforms such as Linux, Windows, macOS, Android, and embedded systems. This toolkit, developed by the widget library, is such a hit because of the tools that are loaded with features to help developers integrate applications that have good user experiences and visual interface.
Key Features of Qt
- Cross-Platform Development: Qt helps the developers of the resultant applications program only once and run these applications across different operating systems without any incompatible changes to the code. This feature promotes the sustainability of those companies that are supposed to fail after years of operation by enabling them to reach more individuals with the lowest possible amount of work.
- Rich UI Capabilities: Qt provides dozens of widgets and tools to the development team to create awesome and modern user interfaces. Capability of this includes supporting and updating of an animation to the output like graphics advancements (e.g., alludes), and been able to touch and vice versa.
- Performance:Qt Is doing well, in terms of performance, and memory savings that. It is of course a bit resource heavy but are ideal for resource tight environments such as embedded systems and mobile devices.
- For the most part, Qt is a flexible out-of-the-box product, with the list of supported programming languages which are the most commonly recognized such as C++, Python, and JavaScript, thus developers could choose the ones that they feel comfortable with the most.
- It is important to note that Qt is very comprehensive in terms of documentation and it also has a large community that is always ready to help developers with their challenges and learn from what others have been through, thus making the programming process a lot of fun and interesting.
How to Use Qt
When you decide to use Qt at Vakoms ( https://vakoms.com/qt/ ) to create and deploy an application, several steps must be taken. The names of the steps are listed as follows: First, you have to set up the development environment. Finally, the last step will be to create and deploy your application, all thanks to the Qt platform.
Step 1: Install Qt
The installation process of Qt is somewhat easy as you first get the software from the company website. After that, you can choose what IDE you want to use, with the package. Besides that, there is also an integrated development environment such as Qt Creator, one of the most popular IDEs used for Qt development that comes in a ready-to-use manner.
Step 2: Set Up Your Development Environment
With This is done after installing Qt. The IDE of Qt is Qt Designer, which besides code editing, has model designer, support, etc. It covers different operating systems, so, a single application can be developed for different systems without changing the IDE.
Step 3: Create a New Project
Begin the project by opening a new window on Qt Creator. You can implement the project using either the Qt Widgets Application, or the Qt Quick Application and so many others that are available. To ensure the template that meets the choice of your project is as easy as possible, simply select the one that suits your project best.
Step 4: Design Your UI
Qt Creator is an IDE that Qt includes, and it enables you to create the user interface for the application by simply dragging and dropping elements. You can add widgets, set properties, and connect signals and slots to attach the behavior of your UI elements
Step 5: Write Your Code
After you have designed the presentation, you are ready to code in your selected programming language. C++ is the main language in Qt, however, developers are not restricted to it, in particular with the availability of PyQT or PySide, which are the Qt versions written in Python.
Step 6: Build and Run Your Application
On the other hand, you will be able to build and execute your application project directly from Qt Creator after you have finished writing the code. When being coded, the IDE contains functions for compilation, testing, and debugging your application, assuring that there are no issues during the development.
Step 7: Deploy Your Application
When your application is all prepared, the Qt libraries present you with the ability to be able to deploy the programs to users through a variety of media. You can build installers for desktop applications or get packages set for mobile and embedded systems. This will make your application easy to distribute via end-users.
Why Choose Qt?
If you are bothered with why you should go for Qt for your apps development, there are good answers to be given. Chief among these is its cross-platform compatibility which saves development time and resources due to the ability to code for multiple OSs with the hang of merely one version only. Its variety of tools and extensive documentation simply the development process, freelancing the developers from creating quality applications is the major factor in his creative capacity.
To boost the effectiveness of Qt in the case of businesses, it is highly recommendable that they involve development teams experienced with Qt. Vakoms software is a company that excels at Qt development and is thus one particularly specializing in Qt. Their skills will help you to have your projects that are developed both with high efficiency and effectiveness through utilizing the Qt framework to the most extent.
Conclusion
Qt is a powerful and flexible framework that makes it easy to develop cross-platform applications with rich user interfaces. Start using Qt and by taking the steps as explained above, you can create applications of high power that will subsequently run on different platforms easily.
TECHNOLOGY
Rediscovering Hobbies: Unique Activities for Seniors

Do you ever feel like trying something new?
For seniors, finding hobbies can be a way to stay active and happy. It’s not just about passing the time; it’s about finding joy and maybe learning a thing or two. From crafting to technology, there’s a world of activities out there.
This guide will explore some unique activities for seniors wanting to add a little excitement to their days. Whether you’re looking for a new challenge or a peaceful pastime, there’s something for everyone.
Gardening With a Twist
Gardening is a top pick among elderly pastimes, but why not give it a twist? Imagine combining music with your gardening sessions.
Listening to your favorite tunes while tending to plants can boost your mood and make the time fly. Or take gardening to a new level by trying aquaponics, where you grow plants and fish together in one system. It’s fun and sustainable, and you might just harvest your dinner!
Start small with a mini aquaponic kit. This way, gardening becomes more than just a hobby; it’s an adventure.
Creative Writing Workshops
Creative writing workshops are fantastic for seniors interested in storytelling. These sessions encourage you to share your life experiences and create new worlds through words. They offer a chance to enhance your writing skills while making new friends who share your passion.
Writing can be a solo activity, but in workshops, it turns into a social event. This form of senior leisure not only stimulates your imagination but also keeps your mind sharp. Start penning your story today and see where it takes you!
Tech Savvy Explorations
Being tech-savvy is not just for the young. Seniors can dive into the digital world too! Learning how to use smartphones, tablets, or computers opens up new opportunities. You can video chat with family, join online clubs or even play games.
There are also classes designed for seniors to make learning easy and fun. Start with basics and soon you’ll be exploring the internet, sending emails, and maybe even making your own blog. Don’t miss out on the tech fun; it’s easier than you think!
Cultural Cooking Classes
Exploring new foods is exciting. In cultural cooking classes, seniors can learn to make dishes from all over the world. It’s not just about cooking; it’s about tasting new flavors and learning about different cultures.
Plus, sharing your creations with friends or family is fun. You might make Italian pasta, Mexican tacos, or Japanese sushi.
Cooking classes are great because you meet people who like trying new things too. Start with one recipe from a country you’re curious about and see where your taste buds take you!
Mindfulness and Movement
Mindfulness and movement activities, like yoga or tai chi, are perfect for seniors. These exercises help keep your body flexible and your mind calm. They’re not too hard, so anyone can try them!
For example, retirement life at Discovery Village Deerwood is about having fun while staying healthy. Doing these exercises can make you feel better every day.
Explore Unique Activities for Seniors Today
Unique activities for seniors are more than just hobbies; they’re gateways to new experiences, friendships, and joys. By exploring different activities, seniors can enrich their lives, stay active, and keep learning. There’s a whole world of unique activities out there waiting to be discovered.
So, why not start today? Make your days brighter and more exciting by trying something new.
For more helpful blog posts like this one, visit the rest of our site!
APPS & SOFTWARE
How Custom Application Development Services Can Enhance User Experience on iOS
Have you ever wondered how some iOS apps are so user-friendly?
Custom application development services make that happen. They fine-tune apps to fit what users need and want. These services help make apps easier to use and more enjoyable.
Keep reading to learn how these services can make your iOS experience better. Get ready to see your app in a whole new way!
Tailored Functionality
Custom development services focus on making apps do exactly what you need. Think of it as getting a suit tailored just for you, rather than buying one off the rack. These services work with you to add features that make the app more useful for your daily activities.
For example, if you use an app for school, developers can add tools that make learning or organizing notes easier. This way, using the app becomes smooth and enjoyable, making your tasks quicker to complete and less of a hassle.
Intuitive Design
An intuitive design means the app looks nice and is easy to use right away. When app developers work on custom apps, they think about who will use the app and how they can make it simple for them. They organize the app so everything is easy to find and use.
For example, the app places buttons and actions where you’d expect them, so you don’t get lost. This makes using the app feel natural – as if you’ve been using it for years.
Performance Optimization
Custom app development does more than just add cool features or make an app look good. It also makes sure the app runs fast and without problems, even if you’re doing a lot on it. Imagine playing a video game with no lag or sending a message and it sends right away.
That’s what we mean by performance optimization. It’s about making sure everything in the app works smoothly and quickly. It makes your experience better because you can do what you need without waiting.
Personalized Content
Custom apps come with a cool feature where the content changes based on what you enjoy or need. It’s as if the app knows you. If you’re using a learning app, it shows subjects you’re into or find challenging.
This keeps you interested because everything feels made just for you. It helps a lot when you’re trying to stay focused or learn something new. This way, using an app becomes more fun and useful, making every minute you spend on it count.
Seamless Integration
Seamless integration means your custom app works well with other apps and devices you use every day, without any trouble. Think of it as when puzzle pieces fit perfectly. This is great because it lets you share information between apps easily.
For instance, if you take a note in your app, it can show up in your calendar app if you have a meeting. Customized software development makes your life easier because everything works together smoothly. It helps you stay organized and on top of your tasks.
Have Custom Application Development Services Enhance User Experience Today
Custom application development services can change how you feel about using apps on iOS. They make apps work better for what you need. From making the app run smoother to fitting your style, these services do it all.
Try custom app development services to improve your apps. Make your phone time more enjoyable and less frustrating.
We hope you found this article helpful. Keep reading our blog for more helpful tips and advice
APPS & SOFTWARE
Stay Ahead of the Curve: Trends in Social Media Growth

In today’s digitally connected world, social media has become an integral part of our lives. From staying in touch with friends and family to discovering new products and services, its influence is undeniable. As technology continues to evolve, so do the trends in social media growth. Let’s explore some of the key trends that are shaping the landscape of social media.
The Rise of Social Media
Historical Background
Social media platforms have come a long way since the early days of MySpace and Friendster. With the advent of platforms like Facebook, Twitter, and Instagram, social media has become a global phenomenon, connecting billions of people around the world.
Impact on Society
The impact of social media on society cannot be overstated. It has revolutionized communication, entertainment, and even politics. From viral trends to social movements, social media has the power to shape public opinion and drive change.
Current Trends in Social Media Growth
Video Content Dominance
One of the most significant trends in social media is the dominance of video content. Platforms like TikTok and YouTube have seen explosive growth, with users consuming billions of hours of video content every day. Thanks to The Techno Tricks behind these platforms, users are immersed in a vast array of engaging and entertaining videos, driving unprecedented levels of user engagement and interaction.
Augmented Reality Integration
Another emerging trend is the integration of augmented reality (AR) into social media platforms. AR filters and effects are becoming increasingly popular, allowing users to enhance their photos and videos with virtual elements.
Ephemeral Content on the Rise
Ephemeral content, which disappears after a set period of time, is also on the rise. Platforms like Snapchat and Instagram Stories have popularized this format, providing users with a more authentic and spontaneous way to share moments.
Influencer Marketing Evolution
Micro-Influencers
Influencer marketing has evolved beyond celebrities to include micro-influencers – individuals with smaller but highly engaged followings. Brands are increasingly turning to micro-influencers for their authenticity and niche appeal.
Authenticity Over Celebrity
Consumers are also prioritizing authenticity over celebrity when it comes to influencer marketing. They want to see real people using products in genuine ways, rather than scripted endorsements from celebrities.
Social Commerce Boom
Shoppable Posts
Social commerce is experiencing a boom, with platforms like Instagram and Facebook introducing shoppable posts that allow users to purchase products directly from their feeds.
Direct Messaging for Sales
Direct messaging is also becoming a powerful tool for sales on social media. Brands are leveraging messaging apps like WhatsApp and Messenger to engage with customers and drive conversions.
Privacy Concerns and Regulation
Data Privacy Laws
With the increasing scrutiny of social media platforms, data privacy has become a major concern. Governments around the world are enacting stricter regulations to protect user data and hold platforms accountable for their practices.
Platform Transparency Measures
Platforms are also taking steps to improve transparency and accountability. From disclosing ad targeting practices to providing users with more control over their data, transparency measures are becoming increasingly important in rebuilding trust.
The Future of Social Media
Emerging Platforms
The future of social media is filled with exciting possibilities. Emerging platforms like Clubhouse and TikTok continue to push the boundaries of creativity and innovation, offering new ways for users to connect and share content.
AI and Personalization
Artificial intelligence (AI) is poised to play a significant role in the future of social media. From personalized recommendations to automated content creation, AI technologies are revolutionizing the way we interact with social media platforms.
Conclusion
As social media continues to evolve, staying ahead of the curve is essential for businesses and individuals alike. By embracing emerging trends and technologies, we can harness the power of social media to connect, engage, and thrive in a rapidly changing digital landscape.

 HOME IMPROVEMENT1 year ago
HOME IMPROVEMENT1 year agoThe Do’s and Don’ts of Renting Rubbish Bins for Your Next Renovation

 BUSINESS1 year ago
BUSINESS1 year agoExploring the Benefits of Commercial Printing

 BUSINESS1 year ago
BUSINESS1 year agoBrand Visibility with Imprint Now and Custom Poly Mailers

 HOME IMPROVEMENT9 months ago
HOME IMPROVEMENT9 months agoGet Your Grout to Gleam With These Easy-To-Follow Tips

 TECHNOLOGY11 months ago
TECHNOLOGY11 months agoDizipal 608: The Tech Revolution Redefined

 HEALTH9 months ago
HEALTH9 months agoThe Surprising Benefits of Weight Loss Peptides You Need to Know

 HEALTH9 months ago
HEALTH9 months agoYour Guide to Shedding Pounds in the Digital Age

 HEALTH12 months ago
HEALTH12 months agoHappy Hippo Kratom Reviews: Read Before You Buy!











