TECHNOLOGY
Casibom: The Digital Alchemy Reshaping Systems, Society, and Self

Introduction: The Word You’ve Never Heard—But Will Never Forget
In the endless swirl of tech buzzwords, acronyms, and conceptual frameworks, it’s rare to stumble across a term that feels like it’s peeking out from the future itself. Casibom is one of those words. It doesn’t just sound like the name of a forgotten utopian city or a futuristic algorithm—it encapsulates a hidden current shaping the way we interact with information, systems, and even each other.
At first glance, Casibom might seem like a cryptic anomaly. But once you begin to unpack its meanings—philosophical, technical, and societal—it becomes clear: this isn’t just a trend. It’s a lens through which we can understand our emerging digital condition.
What Is Casibom?
Casibom is a conceptual framework and decentralized methodology that blends randomized design, human-centric interaction, and adaptive intelligence. It lives at the intersection of digital systems, psychology, and algorithmic evolution.
Think of Casibom as the quantum jazz of technology—structured improvisation. It’s about building systems that embrace unpredictability while remaining intentional, adaptive, and meaningful. Unlike rigid protocols or traditional coding paradigms, Casibom thrives on serendipity engineered with precision.
In real terms, Casibom might describe:
- A decentralized content platform that reshapes itself based on user values rather than clicks.
- A learning system that evolves in tandem with a student’s curiosity.
- A business model that pivots in real time using ethical data triggers and emotional resonance.
Origins: Philosophy Meets Programming
The term “Casibom” is a portmanteau drawn from “Casino” (representing randomness and chance) and “Bombos”, an ancient Greek term for rhythm and echo. This unusual blend reflects the philosophical roots of the concept: entropy meets harmony.
Casibom emerged from a growing discontent with deterministic design systems. It was first coined by speculative futurists in underground digital think tanks exploring post-algorithmic intelligence. Inspired by Deleuze’s rhizomatic theory, quantum computing, and indigenous storytelling frameworks, Casibom became a term to explore the multiplicity of meaning, adaptive design, and the ethics of unpredictability.
Real-World Applications: Where Casibom Is Already Working
In AI and Machine Learning
Casibom-based AI models are beginning to show promise in generative systems that don’t just respond to data but evolve with context. These models prioritize ethical variance, preventing AI from becoming too rigid or exploitative. Imagine a recommender system that nudges you toward balance rather than addiction.
In Education
Learning platforms inspired by Casibom adapt to student emotion and motivation, not just performance metrics. Instead of testing for fixed outcomes, Casibom designs pathways based on curiosity spirals—learning fueled by wonder.
In Design and UX
Casibom principles are leading to interface models that shape-shift based on mood, time, or cultural context. Think of a website that becomes brighter, softer, or more tactile depending on the user’s attention rhythm or emotional state.
In Business Models
Brands applying Casibom logic are experimenting with value-based pricing, fluid identity models, and reputation-led governance. This helps build trust with consumers in a time when static business models often feel hollow.
In Society
Casibom is also surfacing in civic tech, where urban systems (e.g., transportation, energy, voting) adapt to citizen sentiment, reducing friction and enhancing trust.
There’s plenty more where that came from—browse our other helpful content!
Casibom vs. Traditional Systems
| Feature | Traditional Systems | Casibom Framework |
|---|---|---|
| Logic | Deterministic, rule-based | Adaptive, emergent |
| User Role | Passive consumer | Co-creator |
| Feedback | Linear, metric-based | Emotional, multidimensional |
| Design Goal | Efficiency, scalability | Resonance, trust, adaptability |
| Risk Handling | Avoidance, mitigation | Inclusion, transformation |
Where traditional models are built to eliminate unpredictability, Casibom systems weave chaos into the design—not to lose control, but to gain resilience.
Future Implications: Ethics, Risks, and Radical Possibility
The Casibom model is not without challenges. As we dive deeper into adaptive and personalized systems, we must ask:
- Who controls the variance?
- What biases live in the “random”?
- How do we preserve identity in constantly shifting frameworks?
Casibom systems could open the door to ethical surveillance—systems watching over us not to control but to protect. But they could also lead to manipulation cloaked in empowerment. Much like fire, Casibom can either illuminate or burn.
At its best, Casibom fosters systems that breathe with us—organic, forgiving, and alive. At its worst, it may become an excuse for chaos without accountability.
Best Practices: Designing for Casibom
1. Embrace Intentional Uncertainty
Don’t design for fixed outcomes—design for possible states. Let the user become part of the unfolding.
2. Honor Emotional Metrics
Track sentiment, energy, and curiosity—not just clicks and conversions.
3. Build for Interruption and Reentry
Allow users to jump in and out of experiences without penalty, simulating real-world rhythms.
4. Use Ethical Randomization
Inject meaningful surprise—but within boundaries that respect consent and cultural diversity.
5. Prototype with Communitie$s, Not Just Coders
Casibom thrives on co-creation. Include diverse users early in the design process.
Conclusion: Casibom as a Mirror of the Human Condition
Ultimately, Casibom is more than a toolset—it’s a worldview. It acknowledges that humans are not linear beings. We change. We fail. We surprise ourselves. Why shouldn’t our systems reflect that?
In a world increasingly ruled by optimization, Casibom invites us back into the realm of wonder. It reminds us that the most powerful systems are not those that predict—but those that dance, adapt, and evolve.
Casibom doesn’t just power tech. It echoes back something ancient in us: our craving for meaning in the midst of chaos.
Loved this post? You’ll find even more just like it on our blog!
FAQs
1. What is Casibom in simple terms?
It’s a new way of designing digital systems that adapt, surprise, and grow with users—like a smart, emotional computer.
2. Is Casibom a real technology?
It’s more of a concept or framework, but it’s being used in areas like AI, design, and education.
3. How is Casibom different from normal software?
Normal software follows rules. Casibom-based systems are flexible and learn from emotion, behavior, and randomness.
4. Can Casibom be used in business?
Yes! Businesses use it for dynamic pricing, personal customer journeys, and brand trust building.
5. Is Casibom safe to use?
It depends on how it’s built. Like all technology, it needs ethical design to avoid manipulation or bias.
APPS & SOFTWARE
How Sports Apps Can Help You Train Better?
The world of fitness has undergone a revolution. Gone are the days of bulky workout manuals and relying solely on gym memberships. Today, a powerful training tool fits right in your pocket — sports apps.
These versatile apps cater to athletes of all levels and can significantly enhance your training experience. But with a vast array of options available, how do you know which one is right for you? The answer might lie in partnering with an Android app development company to create a customized app that addresses your specific needs and propels you towards your athletic goals.
Let’s explore how sports apps, in general, can be leveraged and how working with a leading Android app development company can take your fitness journey to the next level.
Personalized Plans for Peak Performance
One of the biggest challenges athletes face is crafting a training program that perfectly aligns with their goals and skill level. Struggling to find the right balance between pushing yourself and avoiding injury can lead to frustration and stagnation. Sports apps take the guesswork out of this process by offering personalized workout plans.
Level Up with Customized Programs
Many apps utilize questionnaires to understand your fitness background, goals (e.g., building endurance, increasing strength), and available equipment (gym access, home workout space). Based on this information, they generate custom workout plans tailored to your needs. These plans can be dynamic, adjusting difficulty and exercise selection as you progress. Here’s how these apps achieve personalization:
- Goal Setting: Many apps guide you through a goal-setting process, identifying your desired outcome (increased strength, improved endurance, etc.).
- Skill Level Assessment: Some apps incorporate fitness assessments to gauge your current abilities and tailor workouts accordingly.
- Adaptive Training: As you progress, advanced apps can adjust the difficulty of your workouts based on your performance, ensuring you’re constantly challenged without overtraining.
Finding Your Niche
Sports apps go beyond generic training. Whether you’re a runner aiming for a marathon or a yogi seeking deeper flexibility, there are specialized apps designed for your specific sport. These apps provide targeted routines, drills, and techniques to elevate your skills in that particular discipline.
Staying Injury-Free: Your Virtual Training Partner
Injuries are a major setback for any athlete, derailing progress and motivation. Sports apps can play a crucial role in preventing them by offering valuable injury prevention tips and guidance that go beyond simply listing stretches. They can also offer a cost-effective way to stay injury-free, compared to recurring physical therapy appointments. Some apps even offer motivational features to help you stay focused and positive during your training journey.
Listen to Your Body
Many apps integrate with wearable technology, tracking factors like heart rate, sleep patterns, and workout intensity. By analyzing this data, they can alert you to potential overtraining or improper form that could lead to injuries. This goes beyond simply listing stretches – some advanced apps even:
- Incorporate movement assessments: These assessments can identify muscle imbalances or weaknesses that could lead to injury down the line.
- Provide tailored warm-up and cool-down routines: These routines prepare your body for activity and promote recovery, both essential for injury prevention.
- Offer progressions and regressions: By allowing you to adjust exercises based on your limitations, apps can help you train safely and effectively without pushing your body beyond its capabilities.
Prevention is Key
Several apps offer instructional videos and routines focused on injury prevention. These can include dynamic stretches, mobility exercises, and strengthening techniques to target muscle groups prone to overuse injuries in your specific sport.
Knowledge is Power
The best sports apps go beyond basic exercise instruction. They provide educational content related to common sports injuries, their causes, and rehabilitation techniques. This empowers you to understand your body better and take proactive steps to prevent injuries.
Tracking Your Progress: Motivation Through Data
Staying motivated is key to achieving your fitness goals, and sports apps can be your secret weapon. By allowing you to track your workouts and visualize your progress through valuable tools like graphs and charts, they gamify the experience. Witnessing your improvement over time becomes a badge of honor, keeping you engaged and inspired.
Visualizing Success
Apps meticulously record your workout data, including distance covered, weight lifted, calories burned, and even personal bests. This allows you to see your progress over time in a clear and visually engaging way.
Gamification for Fun
Some apps incorporate gamification elements, awarding points, badges, and virtual rewards for completing workouts and reaching milestones. This playful approach can keep you motivated and add a fun layer to your training routine.
Connecting with the Community
Many apps boast built-in social features that allow you to connect with other athletes. Share your progress, participate in virtual challenges, or even find training buddies to stay accountable and motivated.
How to Choose the Right Sports App for You?
With a plethora of sports apps at your disposal, it’s essential to choose the one that aligns with your specific needs and preferences. However, choosing the right one doesn’t have to be a daunting task. By taking some time to consider your specific needs and preferences, you can find the perfect app to propel you towards your fitness goals. Here are some key factors to keep in mind:
- Your Goals: Are you aiming to build muscle, improve endurance, or train for a specific event? Different apps cater to various goals and offer specialized workout plans.
- Skill Level: Whether you are a seasoned athlete or a complete beginner? Look for apps that offer appropriate difficulty levels and progressions to ensure a safe and effective workout.
- Cost: Freemium models offer basic functionalities, while premium versions often provide more customized plans and features.
- Focus: Does the app cater to your specific sport or offer a more general approach?
- Features: Look for features that resonate with your goals, such as injury prevention tips, performance tracking, or social interaction.
- User Interface: A user-friendly and intuitive interface is crucial for a seamless user experience.
Empowered Fitness: Your Sports App Advantage
Sports apps are more than just glorified workout trackers. They are powerful tools that can personalize your training, guide you toward peak performance, and help you avoid injuries. Imagine having a customized fitness companion readily available – that’s the potential of a well-designed sports app. By leveraging the resources offered by these apps, you can transform your smartphone into a pocket-sized coach that empowers you to achieve your athletic aspirations.
But with so many options on the market, how do you find the perfect fit? That’s why partnering with a reputable sports app development company can be a game-changer. These expert sports app developers can help you identify your specific needs and goals and then craft a personalized app experience that propels you toward success. So, lace up your shoes, download the right app, and get ready to unlock your full potential!

Looking for the best voice changer for gaming, livestream, or live calls? There are two main changers that you will find on the internet which are online or pc program-based. The online voice changer allows users to change their voice without installing any program. On the other hand, the PC-based voice changers have to be installed on the system. By installing a voice changer on a PC you get advantages such as more features like changing voice in real time on other installed programs such as games. This article will guide you on the best voice changers for PC or online.
Part 1. The Best Voice Changer for PC
HitPaw Voice Changer
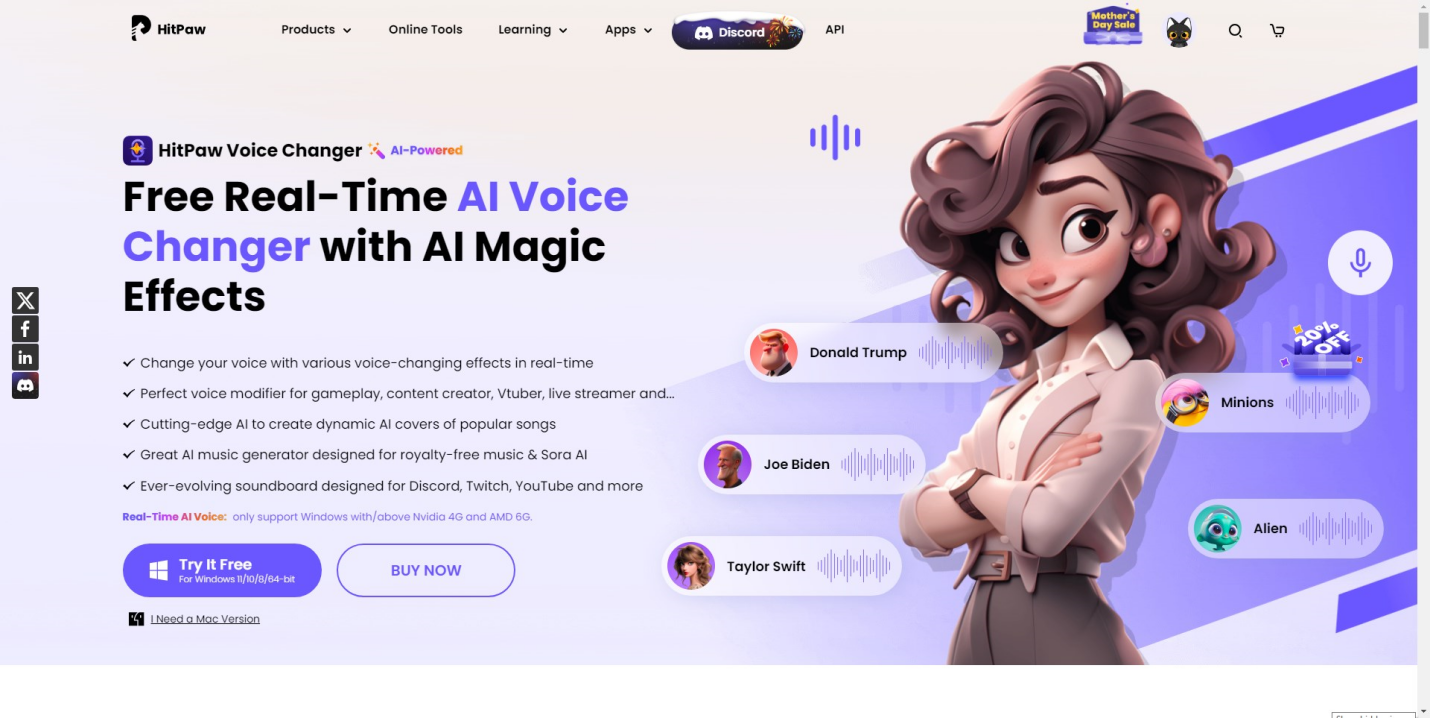
HitPaw Voice Changer is one of the most advanced voice changers for PC and Mac. It features cutting edge AI that allows users to enjoy over 500 voice effects of popular celebrities. The library continuously expands as new voices are added every month. Apart from changing voice Hitapaw also allows users to create custom AI background music. It also comes with a soundboard for livestreaming platforms such as Twitch, Discord, YouTube and many others. Lets take at lookat some of its features.
key features
Free to use: You can download and use the software without paying anything. There might be limitations in the free version compared to paid plans, but it allows you to try out the basic features.
Personalize the voice changer for the PC: Users can set hotkeys on their keyboards to switch to different voices fast during live streams, gaming, or live calls.
Real time voice changer: The best thing about Hitpaw is that you can change your voice in real time. It does all this while utilizing minimalcpu resources
Very beginner-friendly: Hitpaw Voice Changer is designed to be easy to use, even for people with no prior experience with audio editing software.
Various voice characters: It comes with a huge library of character voices from artists, to actors that is continuously updated with more every month.
Other voice changers for PC
MorphVoc
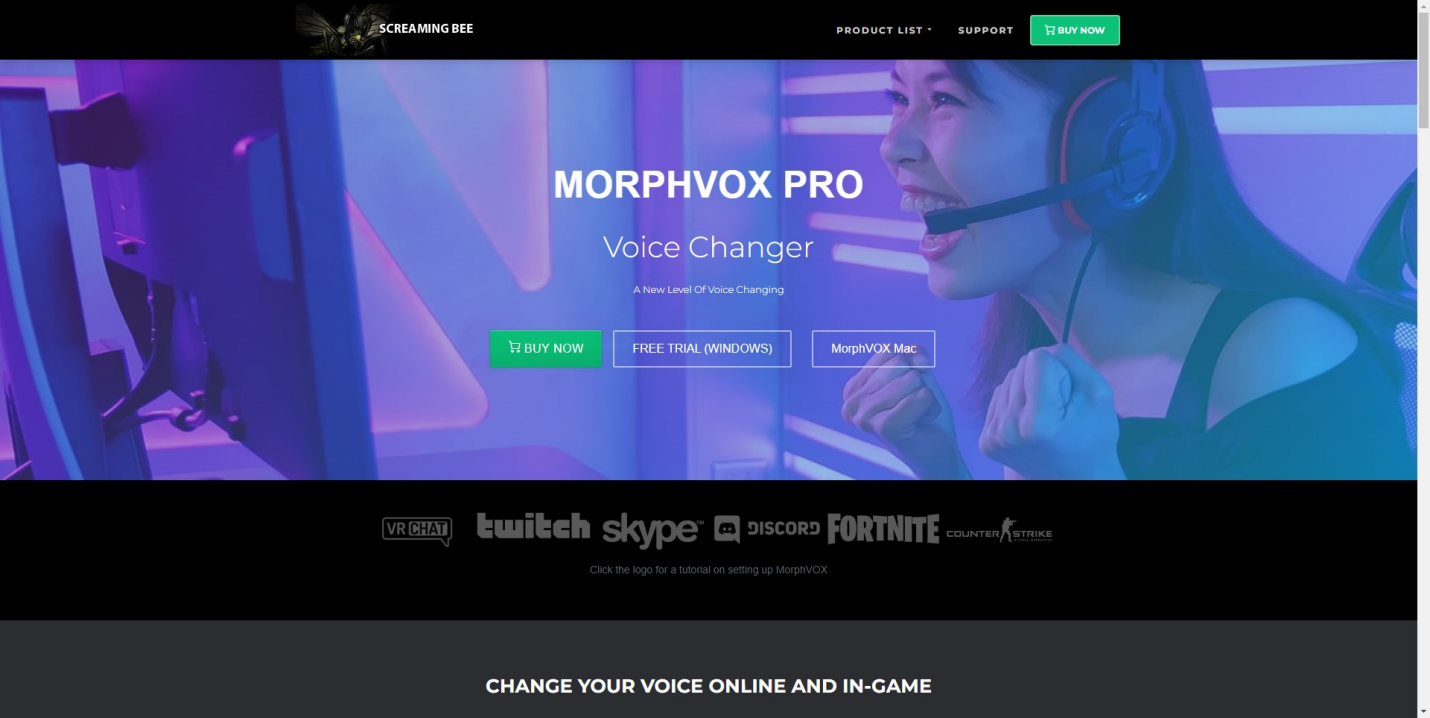
MorphVox is a well-regarded voice changer known for its user-friendly interface and vast library of voice modification options. Perfect for beginners and experienced users alike, MorphVox offers a variety of pre-programmed voices that can instantly transform your voice into a robot, alien, or even make you sound like the opposite gender.
Features
Preset voices: MorphVox offers a wide range of pre-programmed voices like robot, alien, and male-to-female.
Voice creation tools: Allows you to fine-tune existing presets or create custom voices by adjusting pitch, formant (resonance), and effects.
Soundboard: This lets you add sound effects to your voice alongside the voice modification.
Voicemeeter
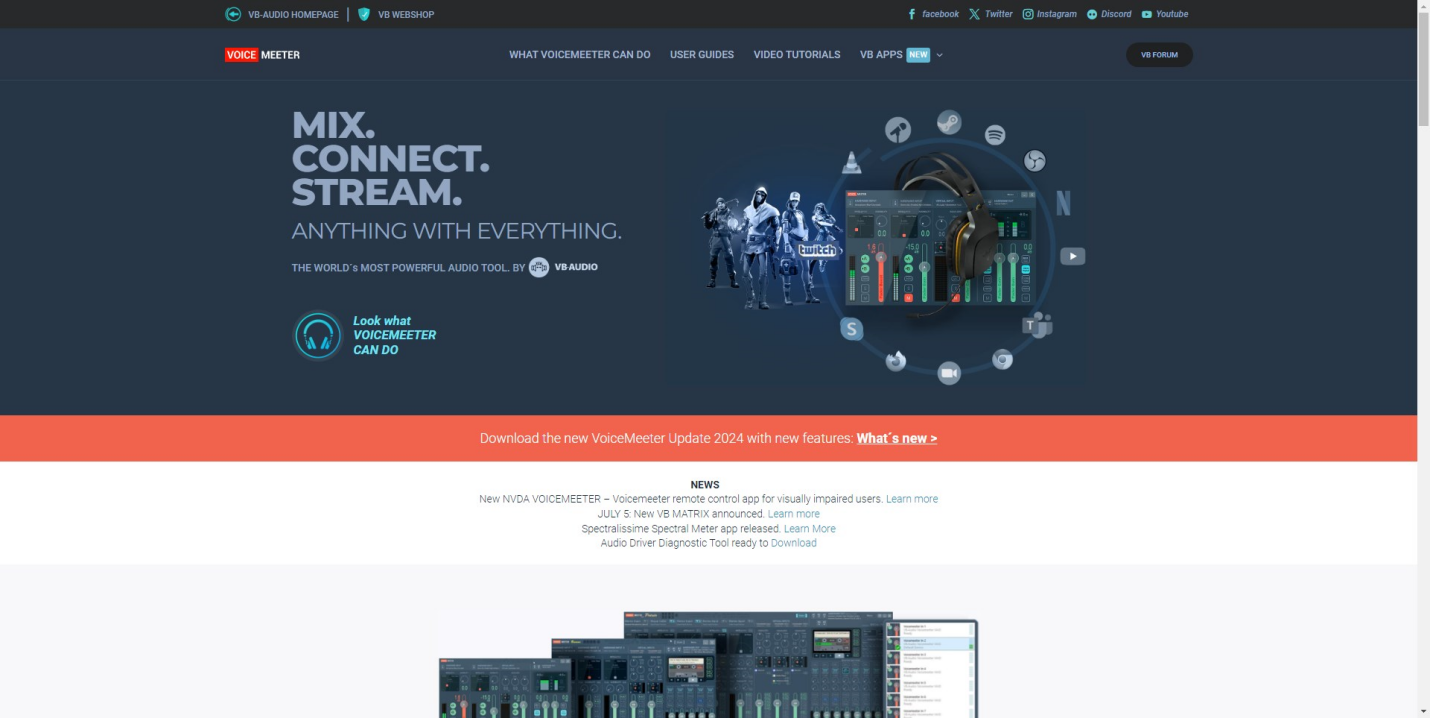
Voicemeeter is more than just a voice changer; it’s a powerful audio mixing application with built-in voice manipulation capabilities. It provides extensive control over your computer’s audio inputs and outputs, allowing you to mix and manipulate sounds from your microphone, games, and other applications with incredible precision.
Features
Advanced audio routing: Offers extensive control over your computer’s audio inputs and outputs, allowing you to mix and manipulate multiple audio sources.
Voice effects: Provides basic voice modification features like pitch shifting and EQ. (Equalization – adjusting different frequency ranges)
VST support: Lets you integrate additional virtual instruments or effects plugins (VST) for more advanced voice manipulation (Requires additional software purchase).
MagicMic
MagicMic is a user-friendly voice changer designed specifically for streamers and content creators who want to add excitement and entertainment to their broadcasts. Streamlining the process for live voice modification, MagicMic offers a variety of voice filters and effects that can be applied in real time while you’re streaming or recording.
Features
Real-time voice effects: Offers a variety of voice filters and effects that can be applied live while streaming or recording.
Voice library: Provides access to a collection of pre-recorded voices and sound effects.
Voice morphing: Allows you to blend your voice with different characters or sound effects for unique audio combinations.
Clownfish

Clownfish offers a basic set of voice modification tools that can still add a fun element to your audio projects. It allows you to adjust the pitch of your voice to sound higher or lower, and add echo effects for a more dramatic touch. Clownfish also comes with a basic voice recording function, so you can capture your voice with the applied effects and share it with others.
Features
Voice effects: Offers voice modification options like pitch shifting and echo.
Voice recording: This allows you to record your voice with the applied effects.
Customization options: While limited, it lets you adjust some parameters of the voice effects.
Part 2. The Best Voice Changer for Online
Voicechanger.io
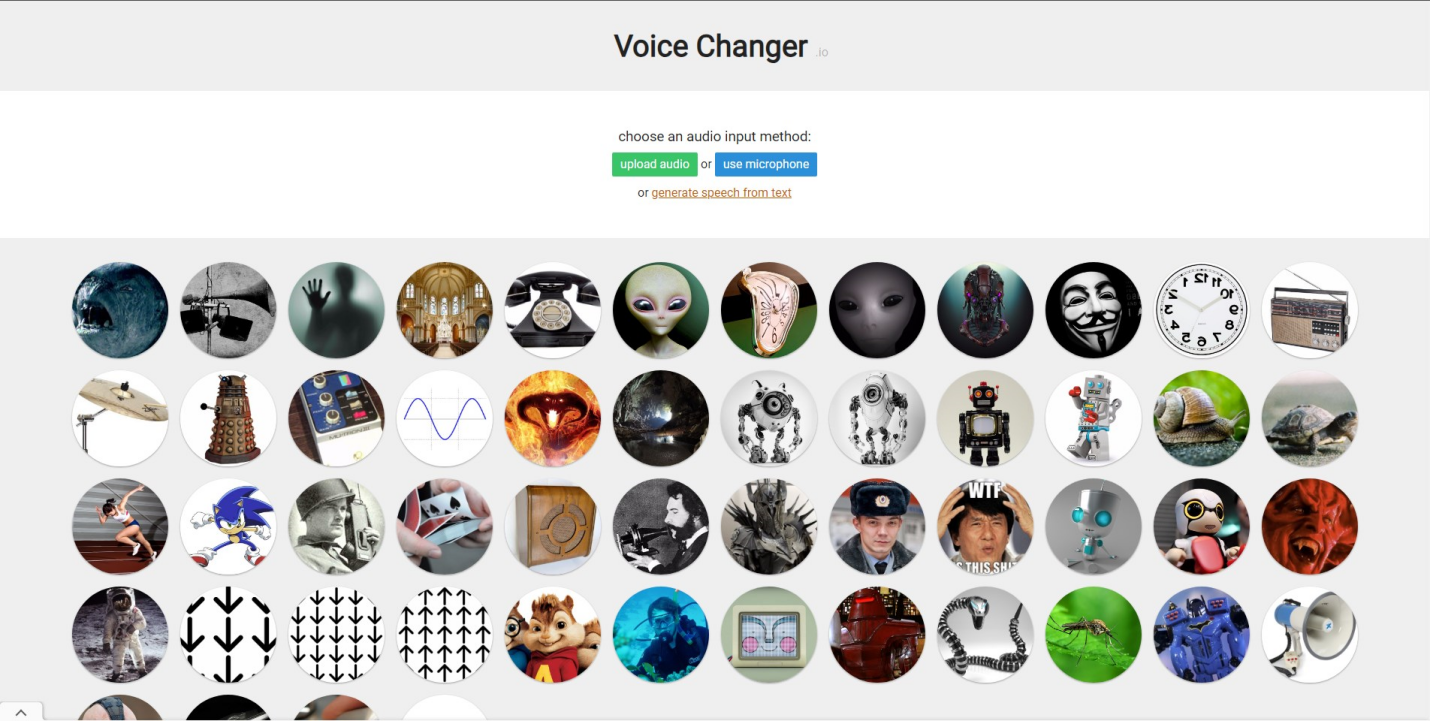
Voicechanger.io is a free online tool that lets you modify your voice recordings. You can use it to change the pitch of your voice, making it sound higher or deeper, or add effects like making it sound like a child, robot, or even Donald Duck. It’s a simple tool for having fun with your voice or potentially anonymizing it for short recordings.
Media.io Online Voice Changer
Media.io offers an online voice changer that utilizes AI technology. You can upload audio or video files and modify the voices within them. This tool allows for pitch adjustments, potentially creating subtler or more dramatic vocal transformations. There’s also the option to explore various voice effects.
Murf

Murf.Ai steps beyond basic voice changing, offering an AI-powered text-to-speech experience. Instead of modifying existing recordings, you provide your script and Murf.Ai generates a voiceover from scratch. With a library of diverse voices in multiple languages and accents, you can pick the perfect tone to match your project.
Conclusion
You can change your voice to sound like your favorite movie character, artist, or celebrity. To achieve this you need a voice changer for PC or one that is online based. Each of these two options has its own advantages. If you are looking for the best voice changer for PC then you need to try HitPaw. It’s easy to use, affordable and contains one of the most realistic voices on the market.
FAQs
Can I make my voice sound like a girl?
Yes, You can make your voice sound like a girl using a voice changer for PC and online. Some voices are preset by cloning the voices of popular celebrities. While others are AI-generated from training made from many different voices.
What makes a girl’s voice?
A girl’s voice is characterized by higher pitch, smoother intonation, and softer articulation compared to a masculine voice. It often involves speaking with a more melodious tone and using a wider vocal range, reflecting societal perceptions of femininity in speech patterns.
Can a guy fake a girl’s voice?
It’s very easy to fake a girl’s voice as a guy. All you need is a voice changer with a realistic voice. Most of the platforms have a huge library with different girl voices that you can choose from
APPS & SOFTWARE
Navigating the Sales Funnel: 6 Best Practices for Effective Selling

Many people are quick to associate the term “sales funnel” with software solutions designed to aid marketing campaigns. Well, it is worth mentioning that “sales funnel” as a concept existed long before these software solutions came to be. For the sake of providing a better perspective, these software solutions came into the picture a little over a century after the concept was introduced.
Be that as it may, they have revolutionized the concept. They have made it more practical and result-yielding. You can see Clickfunnels for more information on how they are capable of doing this. However, the right sales funnel software solution must be chosen when the need arises.
Having made this clear, you also need to be aware of the basics. This is so that your marketing goals will be met and even exceeded.
Sales Funnel Tips for Maximum Conversion
Quite a lot has happened since sales funnel software solutions came to the fore. However, that does not rule out the need for knowledge of the basics.
It even puts you in a better position to make the most of these digital tools. To this end, some tips for maximum conversion with your sales funnel campaign are discussed below:
Be Aware of Your Audience
Every brand, product, or service has its target audience(s). These are the prospects that are the best fit to become customers.
They are important in the grand scheme of things and your knowledge of them is supposed to influence your subsequent decisions. Running a marketing campaign without having a clear understanding of who they are is like journeying without a destination in mind.
Knowing your ideal target audience is important, but it does not stop at that. You need to understand these personas in the best way possible. Some of the things to know about them include their:
- Pain Points
- Needs
- Preferences
- Purchase Journey
- Competitive Landscape – How it affects your target audiences
- Communication Preferences
- Challenges & Goals
- Behavioral Patterns
- Demographics
- Psychographics
- Buying Motivation
The above-listed might seem like quite a lot. However, it goes to show how important knowing and understanding your target audiences are. So, put in the work to get this crucial information.
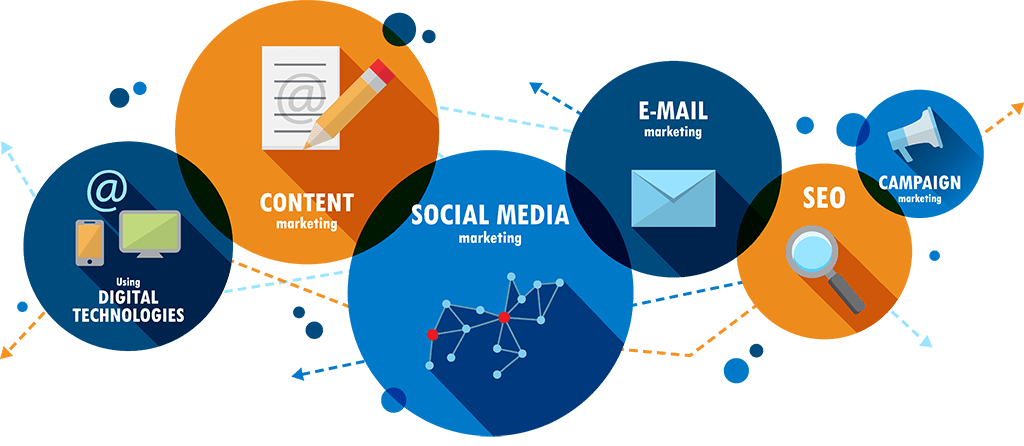
Use Engaging Content
Engaging your leads is one of the best ways to eventually bring them on board. This is why you should not have a problem with feeding your prospects with engaging content.
Once again, it takes knowledge and a deep understanding of who your target audiences are to offer them very engaging content. Speaking of engaging content, some of the options that can be explored include:
- Videos
- Blog Posts
- Webinars
- Social Media Content
Various content forms can be engaged as seen above but the goal remains the same. It is about offering valuable and relevant insights that address your target audience’s challenges.
However, it should be noted that some content forms are more promising in their ability to help in actualizing this goal. So, make an informed decision when choosing your content form.
Build Relationships
There would always be that generalized feel with content forms. This is not to say that they are not good.
However, there comes a time in the marketing campaign when your prospects need to feel like you are communicating with them. This is instead of the feeling that you are communicating with every one of their kind.
Personalized interactions have to come in at this point. This would go a long way in building the trust that you need from your prospect’s end.
To do this, active listening is a necessity. Furthermore, there must be a clear display of empathy. So, every possible and reasonable means to achieve these should be explored.
Lead Qualification
The term leads is more ambiguous than many marketers/people know or would like to admit. To provide a better perspective, you might want to liken the term lead to the term learner/student.
A kid in grade 4 is a learner/student. The same goes for an adult running a postgraduate degree in a reputable college. However, some things can be taught the latter but not the former.
In the same vein, you cannot afford to treat/nurture all your leads the same way. They have varying levels of interest in your marketed product, service, or brand.
This is why you need to do something known as lead Qualification. It is all about categorizing your leads. Of course, this is mostly based on their level of interest in your product, service, or brand, as the case may be. Besides the level of interest, other bases for lead qualification include:
- Budget
- Need
- Fit
- Authority
- Timeline
- Engagement
- Buying Signals
- Existing Relationships
A scoring model is required to do a good job of qualifying leads. Presenting very highly relevant and persona-revealing questions before leads is one of the ways to get the job done.
Be Solution-Driven
Your ultimate goal is selling products and/or services. This is unless your campaign is solely about brand awareness.
Be that as it may, you do not want to come off as hell-bent on selling your products or services before your leads. This usually paints the picture of a brand that would do anything to get money, including being deceptive.
Rather, you want to appear as a brand more interested in offering solutions to your target audience’s challenges through your products and/or services. This way, it is a win-win for everyone – you and your leads. So, this should be your mindset at every point in your marketing campaign.
Monitor & Use Analytics
You need to make it a point of duty to regularly monitor and make informed decisions based on key metrics. This includes things such as sales velocity, customer acquisition, and conversion rates.
Wrap Up

The chances of running a successful marketing campaign are likely when the right sales funnel software solution is used. However, this does not rule out the need to understand the basics of running a successful marketing campaign.
Knowledge of the basics even ensures that the most is made of these software solutions. To this end, the basics shared here should be taken seriously.

 HOME IMPROVEMENT1 year ago
HOME IMPROVEMENT1 year agoThe Do’s and Don’ts of Renting Rubbish Bins for Your Next Renovation

 BUSINESS1 year ago
BUSINESS1 year agoExploring the Benefits of Commercial Printing

 BUSINESS1 year ago
BUSINESS1 year agoBrand Visibility with Imprint Now and Custom Poly Mailers

 HOME IMPROVEMENT9 months ago
HOME IMPROVEMENT9 months agoGet Your Grout to Gleam With These Easy-To-Follow Tips

 TECHNOLOGY11 months ago
TECHNOLOGY11 months agoDizipal 608: The Tech Revolution Redefined

 HEALTH9 months ago
HEALTH9 months agoThe Surprising Benefits of Weight Loss Peptides You Need to Know

 HEALTH9 months ago
HEALTH9 months agoYour Guide to Shedding Pounds in the Digital Age

 HEALTH12 months ago
HEALTH12 months agoHappy Hippo Kratom Reviews: Read Before You Buy!









