GENERAL
Savastan0: What Sales Mean for Fullz CC Dump Online Security
Introduction to Fullz CC Dumps
In the ever-evolving landscape of online security, a new threat has emerged that demands our attention: Fullz CC dumps. These digital goldmines contain sensitive personal information and pose significant risks to individuals and businesses alike. But what do these dumps mean for your safety in cyberspace?
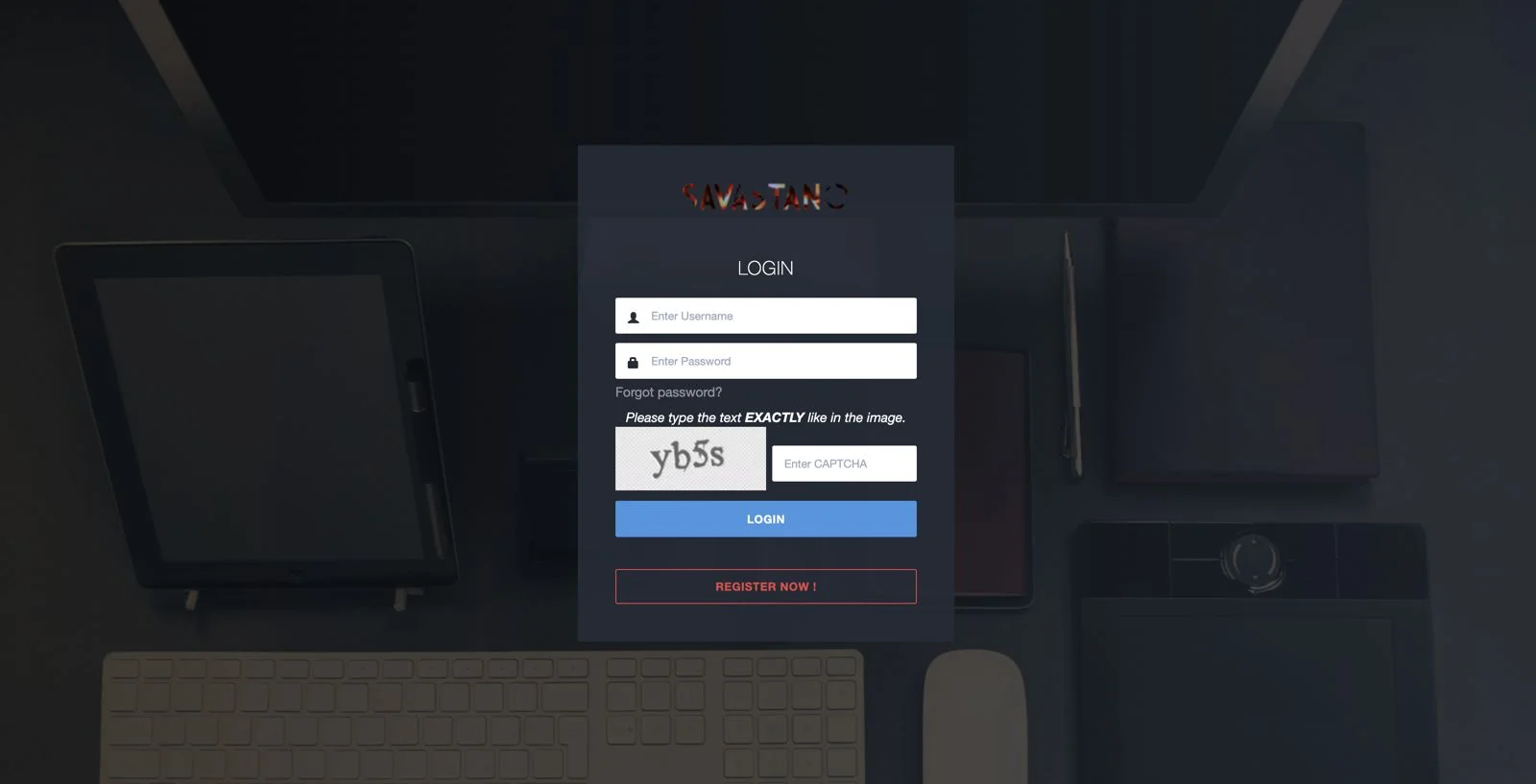
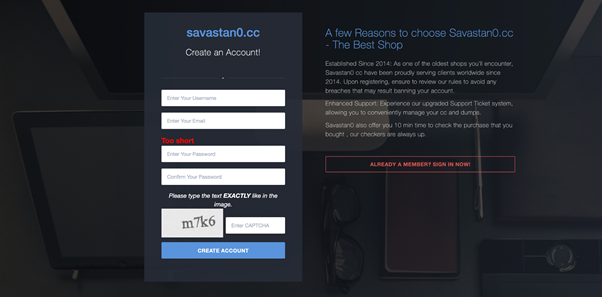
Recently, sales from notorious sources like Savastan0 have shed light on just how vulnerable we can be. As cybercriminals grow bolder with their tactics, understanding the implications of such sales becomes crucial for safeguarding your identity. Let’s dive into the world of Fullz CC dumps and unravel the dangers they present to us all.
The Impact of Savastan0 Sales on Online Security
The rise of Savastan0 sales has sent shockwaves through the online security landscape. This notorious marketplace specializes in Fullz CC dumps—comprehensive packages containing personal information and credit card details.
Hackers are leveraging these dumps to execute identity theft and financial fraud on a massive scale. As cybercriminals become more sophisticated, the threat level increases significantly for unsuspecting individuals.
Businesses are not immune either; they face potential data breaches that can lead to devastating financial losses and reputational damage. The growing availability of Fullz CC dumps means that both consumers and companies must remain vigilant.
Each transaction made through platforms like Savastan0 deepens the crisis, making it essential for everyone to enhance their cybersecurity measures immediately. Awareness is crucial now more than ever as this trend continues to evolve with alarming speed.
What Information is Contained in a Fullz CC Dump?
Fullz CC dumps are treasure troves for cybercriminals. They contain a wealth of personal information about individuals.
Typically, these dumps include names, addresses, and phone numbers. This basic data is often paired with financial details like credit card numbers and expiration dates.
What’s more alarming is the presence of Social Security numbers in many cases. This combination allows criminals to create realistic profiles that can be used for identity theft.
Additionally, some Fullz CC dumps may have account login credentials for various online services. These can lead to unauthorized access if not properly secured.
The sheer volume of sensitive information makes Fullz CC dumps particularly dangerous. Each entry represents a potential victim whose life could be disrupted by fraud or theft.
The Risks of Using Savastan0 Fullz CC Dumps
Using Fullz CC dumps comes with significant risks. For one, these dumps contain sensitive personal information that can lead to identity theft. When cybercriminals acquire this data, they can impersonate individuals and drain their finances.
Additionally, engaging in the purchase or use of Savas-stan0.cc Fullz CC dumps is illegal. It exposes users to potential criminal charges and hefty fines. Law enforcement agencies are cracking down on such activities more than ever.
Moreover, online platforms are becoming increasingly vigilant about detecting fraudulent transactions. If you’re caught using a Savastan0 Fullz dump, your accounts may be suspended or permanently banned.
Beyond legal repercussions, there’s also the danger of financial loss due to scams within the underground market itself. Many sellers promise high-quality dumps but deliver nothing or stolen goods instead. The risks far outweigh any perceived benefits associated with using these illicit resources.
How Savastan0 Sales are Affecting Individuals and Businesses
The rise of Savastan0 cc sales is sending shockwaves through both individuals and businesses alike. As these transactions become more prevalent, the threat landscape grows increasingly complex.
Individuals are finding their personal information compromised. When fullz CC dumps circulate in dark web markets, identity theft becomes a real concern. Victims often discover fraudulent charges long after the damage has been done.
Businesses face dire consequences as well. With sensitive customer data at risk, companies must grapple with potential breaches that could lead to significant financial losses and reputational harm. The trust between consumers and brands hangs by a thread when such threats loom large.
Moreover, organizations may incur steep costs related to mitigation efforts. Implementing new security measures or dealing with legal repercussions can strain resources significantly. It’s essential for everyone to stay informed about these emerging threats in today’s digital landscape.
Steps to Protect Yourself from Fullz CC Dumps
Protecting yourself from Savastan0 Fullz CC dumps requires a proactive approach. Start by using strong, unique passwords for all your accounts. A password manager can help you keep track of these.
Savas-stan0.cc Enable two-factor authentication wherever possible. This adds an extra layer of security that makes it harder for cybercriminals to access your information.
Regularly monitor your bank statements and credit reports. Early detection is key in identifying unauthorized transactions or identity theft.
Be cautious when sharing personal information online. Limit what you post on social media, as even seemingly harmless details can be exploited.
Stay updated with the latest security software and ensure it’s always activated. Firewalls and antivirus programs help shield against potential threats.
Educate yourself about phishing scams. Recognizing suspicious emails or links will decrease the likelihood of falling victim to deceptive tactics used by hackers like those behind Savastan0 sales.
Conclusion: Staying Vigilant in the Age of Cyber Crime
As the world becomes increasingly interconnected, the threats posed by cybercriminals continue to grow. The rise of fullz CC dumps, particularly through platforms like Savastan0, serves as a stark reminder of how vulnerable our personal information can be. Individuals and businesses must remain vigilant against these dangers.
Cybersecurity is no longer just an IT concern; it’s a critical component of everyday life. By being proactive—understanding what information is at risk and implementing necessary precautions—you can guard yourself against potential breaches. This includes regularly monitoring accounts, using strong passwords, and employing two-factor authentication wherever possible.
The battle against cybercrime requires constant awareness and adaptation. Staying informed about emerging threats like those associated with Savastan0 login will empower you to take control over your digital safety.
Always remember that safeguarding your data is not just about technology but also about cultivating good habits online. Engage in discussions about cybersecurity with friends or colleagues to spread awareness further.
Being cautious today could save you from significant troubles tomorrow. Maintain that vigilance: it’s essential in this rapidly evolving digital landscape where threats are always lurking around the corner.
FAQ’s
What is Savastan0, and why should I be concerned about it?
Savastan0 is a powerful and innovative security software that aims to protect your devices and online identity from cyber threats. With its advanced features and constant updates, it ensures the safety and privacy of your personal information, financial data, and digital activities.
How can I tell if my personal information has been compromised in a savas-stan0.cc sale?
Your personal information is our top priority and we take all necessary measures to protect it during every transaction. In the rare event that there is a security breach, our team will immediately notify all affected customers and provide them with steps to safeguard their information.
We also have advanced security features in place to prevent any unauthorized access to your data. Rest assured, your safety and privacy are our utmost concerns at Savastan0.
What steps can I take to safeguard my online accounts against potential threats from the dark web?
As technology advances, so do the risks and threats to our online accounts. Fortunately, with Savastan0, you can feel confident in protecting your personal information and accounts from the dangers of the dark web.
Our advanced security features use cutting-edge technology and algorithms to detect any suspicious activity on your accounts.
Are there specific signs that indicate my data might be for sale on the dark web, linked to savas-stan0.cc?
As a user of savas-stan0.cc, you can rest assured that our advanced security measures and constant monitoring make it highly unlikely for your data to be compromised. However, if you do notice any suspicious activity or receive any unusual notifications from your financial institutions, it is always best to contact our support team immediately.
We also recommend regularly changing your login credentials and enabling two-factor authentication for added protection. With Savastan0, you can trust that we prioritize the safety and privacy of our users’ data above all else.
How can savas-stan0.cc like ours help prevent further data breaches in the future?
At Savastan0, we understand that data security is a major concern for individuals and businesses alike. Our product offers advanced encryption and protection measures to safeguard your sensitive information from cyber attacks.
In addition, we constantly update our software with the latest security protocols and conduct thorough vulnerability testing to identify and fix any potential weaknesses.
GENERAL
Empowering Growth: Individual Counseling for Adults Explained

Individual counseling for adults is a powerful tool for personal growth. It helps you learn more about yourself.
In these sessions, you talk to a trained therapist one-on-one. This safe space allows you to explore your thoughts and feelings. Many adults find it useful for managing stress, anxiety, or depression.
Personal goals can also be achieved through counseling. You can develop better coping strategies and enhance your well-being. In this blog post, we will look into the various aspects of individual counseling for adults, providing insights into its benefits, process, and impact.
Benefits of Individual Counseling for Adults
Individual counseling offers a wide range of benefits that can positively impact your life. Some of the benefits include:
Personalized Support and Therapeutic Guidance
Counseling offers personalized support tailored to your unique needs. This approach ensures that your unique challenges are addressed effectively. It also helps in setting realistic and achievable goals.
Therapeutic guidance involves learning new ways to handle life’s challenges. The therapist offers tools and strategies to manage stress and improve mental health. This support can lead to better emotional well-being.
Safe Space for Self-Exploration
Counseling provides a safe space where you can explore your thoughts and feelings. This environment is free from judgment, allowing you to be open and honest. It helps you understand yourself better and find clarity.
In this safe space, you can talk about things that are hard to share with others. The therapist listens and offers psychological support. This can lead to personal growth and healing.
Improved Coping Skills
Counseling can help you develop better coping skills. These skills are useful for managing stress and dealing with life’s challenges. Improved coping skills can enhance your overall well-being and emotional health.
Therapists teach techniques to handle difficult emotions and situations. You can learn how to stay calm during stressful times. Better coping skills lead to a more balanced and fulfilling life.
Confidentiality
Confidentiality is a crucial part of individual counseling. What you share with your therapist stays private. This helps create a safe and trusting environment.
Therapists follow strict rules to protect your privacy. This allows you to speak freely and honestly, knowing that your privacy will be protected. Confidentiality can also provide a sense of safety and trust within the therapeutic relationship.
The Process of Individual Counseling for Adults
Each individual counseling session is unique, depending on your specific needs and goals. However, here are some common elements that you can expect in the process:
Initial Assessment
During the initial assessment, the therapist will gather information about your history and current issues. This helps in understanding your unique situation and needs. The therapist may ask about your background, lifestyle, and mental health.
This first meeting is also an opportunity for you to ask questions. You can discuss your goals and what you hope to achieve through counseling. Building rapport with the therapist is crucial at this stage.
Building Trust
Building trust with your therapist is important for successful counseling. Trust allows you to share your thoughts and feelings openly. This honesty helps the therapist understand and support you better.
Your therapist will work to create a safe space for you to open up and share your thoughts and feelings. This may take some time, but it is essential for effective counseling.
Identifying Goals
Identifying your goals is a key part of the counseling process. Goals help you focus on what you want to achieve. Your therapist can help you set clear, realistic goals.
These goals can be related to personal growth, improved relationships, or better mental health. Knowing your goals makes it easier to track your progress. It also helps your therapist create a plan tailored to your needs.
Using Various Techniques
In individual counseling, therapists use various techniques to help you. These can include cognitive-behavioral therapy (CBT) and mindfulness. Each technique is chosen based on your needs.
Therapists also use techniques such as talk therapy and role-playing. These methods can help you understand and change your behavior. Using these techniques, you can develop better coping skills and improve your mental health.
Regular Check-ins
Regular check-ins with your therapist are important. They help track your progress and make sure you’re on the right path. These sessions can be weekly or bi-weekly, depending on your needs.
During check-ins, you discuss what’s working and what’s not. This feedback will help the therapist adjust your plan. Regular check-ins ensure that you are making steady progress toward your goals.
Finding Accessible and Professional Help
Finding professional help can sometimes be challenging. This is due to location or financial reasons. There are accessible resources available online.
If situations like panic attacks have been causing distress in your life, you can visit Relevance Behavioral Health for assistance. Remember, seeking help when needed is a vital part of maintaining good mental health.
The Impact of Individual Counseling for Adults
Individual counseling can have a significant impact on various aspects of your life, including:
Improved Mental Health
Many people seek individual counseling to manage mental health concerns such as anxiety, depression, or trauma. Through counseling, you can learn how to cope with these challenges and improve your overall mental health.
Increased Self-Confidence
Individual counseling can help you develop a more positive self-image and increase your self-confidence. As you become more self-aware and learn new coping strategies, you may feel more empowered to take on challenges and achieve your goals.
Enhanced Well-Being
By addressing underlying issues, learning healthy coping skills, and improving relationships, individual counseling can enhance your overall well-being. This can lead to a more fulfilling and satisfying life.
The Transformative Power of Individual Counseling for Adults
Individual counseling for adults has a transformative power that can greatly enhance various aspects of your life. By providing personalized support, a safe space for self-exploration, and improved coping skills, counseling can lead to significant personal growth. It can also improve mental health, boost self-confidence, and foster better relationships.
If you’re facing challenges or aiming for personal growth, individual counseling for adults can be a valuable tool to help you achieve your goals and improve your overall well-being.
Did this article help you? If so, take a look at some of our other blog posts) for more informative reads.
GENERAL
Tree Risk Assessment: Ensuring Safety and Health of Your Trees

Tree risk assessment is like a health check-up for trees. Experts look at trees to find any problems that could make them fall or break. They check things like how strong a tree is if it has any diseases, and how it might affect the things around it if it were to fall.
This helps keep people and buildings safe. In this blog, we will discuss how to ensure the safety and health of your trees with a tree risk assessment.
Signs of Tree Health Issues
Identifying signs of tree health issues early can make a big difference. One clear sign is when the leaves turn yellow or brown and fall off earlier than they should. This can mean the tree isn’t getting enough water or has a disease.
Another symptom to watch out for is fungi, like mushrooms, growing at the tree’s base. This often indicates the roots or the internal parts of the tree are weak and rotting. If you see this, it’s a signal that the tree’s health might be in danger and needs attention.
Cracks or splits in the tree’s trunk are serious warning signs. They can show that the tree is struggling and could be close to falling. Regular checks for these signs can help catch problems early and keep the tree and everything around it safe.
Evaluating Tree Structure
Evaluating tree structure is an important step in risk evaluation. Experts look at how a tree’s branches and roots are growing to see if there are any problems. They check to make sure the tree is balanced and not likely to fall over.
Sometimes a tree’s limbs might be too heavy or weak, which can make them dangerous. The experts will look for branches that are dead or dying because these could fall and hurt someone or something. They also check the roots to make sure they are strong and healthy, as sick roots can make a tree unstable.
By doing these checks, people can help keep trees healthy and safe. It’s important to catch any issues early before they become big problems. This helps make sure trees can live a long time without being a danger to people or buildings around them.
Environmental Factors
Environmental factors play a big role in the health of trees. These include the weather, how much water the tree gets, and the soil it’s planted in. Bad weather, like too much rain or not enough, can make trees weak.
Sometimes, trees get too much sunlight or not enough fresh air, which can also affect them. Pollution from cars and factories can harm trees, making them sick. It’s important to watch these factors to keep trees strong and healthy.
Trees need the right mix of conditions to grow well. If the environment around them changes too much, it can be harmful. That’s why taking care of our environment helps trees stay healthy too.
Mitigation Strategies
Mitigation strategies help stop tree problems before they get big. One way is to water trees properly because too much or too little water can hurt them. It’s also smart to use mulch around the base to keep the soil moist and not too hot.
Pruning dead or weak branches is another key strategy. This helps the tree grow strong and stops branches from falling and causing damage. Experts should do this job to make sure it’s done right and safely.
Planting trees in the right spot is very important too. Some trees need more sunlight than others, and putting them in the right place can make a big difference. By choosing the right location, trees can live longer, healthier lives without causing problems.
Monitoring and Maintenance
Monitoring and maintenance are key to keeping trees healthy. This means checking trees often to catch any problems early. Property management teams can help by watching for signs of stress or disease in trees.
When trees get the right care, they stay strong and can live a long time. This includes pruning them and making sure they get enough water. People should make a plan to look after their trees all year round.
This way, trees won’t become a danger to people or buildings. Getting experts to check trees can also save money in the long run. It’s all about keeping our environment safe and green.
Disease and Pest Management
Diseases and pests can cause significant harm to trees, affecting their overall health and stability. That’s why it’s essential to have a disease and pest management plan in place.
Regular monitoring and early detection of any diseases or pests can help prevent them from spreading to other trees. Treatment methods should also be carefully considered, as some chemicals used in treatment can harm the tree and its surroundings.
Proper maintenance practices can also help prevent the spread of diseases and pests. Pruning dead or diseased branches, keeping the area around the tree clean, and promoting overall tree health through proper watering and fertilization can all play a role in disease and pest management.
Role of Professional Arborists
Professional arborists are tree experts who know everything about tree health and safety. They use their skills to check if trees are sick or could fall and cause problems. When there’s a big storm and trees get knocked down, they offer an emergency tree removal service to keep everyone safe.
They also help by advising on how to take care of trees, so they grow strong and healthy. Arborists can figure out the best way to cut dead branches or treat diseases without hurting the tree. By doing this, they help trees live longer and keep our neighborhoods looking beautiful.
Ensuring a Greener Tomorrow Through Tree Risk Assessment
Tree risk assessment is a crucial tool for ensuring the safety and health of our trees. By regularly monitoring and evaluating tree structures, considering environmental factors, implementing mitigation strategies, and seeking professional help when needed, we can keep our trees strong and thriving.
This not only benefits the environment but also helps protect people and buildings from potential dangers. So let’s make sure to take care of our trees and continue to enjoy the many benefits they provide for generations to come.
If you find this article helpful, check out our blog for more informative content.
GENERAL
Understanding the Different Types of Old Dogs Seizures

As our canine companions age, they may face various health challenges, including the onset of seizures. Witnessing your dog experience a seizure can be a frightening and overwhelming experience.
However, understanding the different types of old dog seizures and knowing how to respond can make a significant difference in seizure management and improving their quality of life. Read on
What Are Seizures?
Seizures, also known as convulsions or fits, are sudden, uncontrolled electrical disturbances in the brain that can cause changes in behavior, movement, sensation, or consciousness. They can last from a few seconds to several minutes and vary in severity. Seizures in older dogs can result from a variety of causes, including:
- neurological disorders
- metabolic imbalances
- toxins
- underlying health conditions
Types of Seizures in Older Dogs
Dog owners needs to understand the different types of seizures that can occur in aging dogs to provide appropriate seizure treatment and care. Here are some seizure types.
Generalized (Grand Mal) Seizures
Generalized seizures, also known as grand mal seizures, are the most common type seen in dogs. These seizures involve both sides of the brain and typically lead to a loss of consciousness. Seizure symptoms may include:
- Convulsions or violent shaking
- Stiffening of the muscles
- Drooling
- Involuntary urination or defecation
- Paddling of the legs
These seizures usually last between one to three minutes. After the seizure, dogs may experience a postictal phase, characterized by confusion, disorientation, and lethargy.
Focal (Partial) Seizures
Focal seizures, also known as partial seizures, originate from a specific area in the brain and can manifest in various ways depending on the affected region. Symptoms may include:
- Twitching or jerking of a specific body part (e.g., one leg or side of the face)
- Unusual behaviors such as snapping at the air, chewing motions, or frantic running
- Sudden changes in behavior, such as aggression or fear
Focal seizures can last from a few seconds to a couple of minutes. In some cases, they may progress to generalized seizures.
Psychomotor Seizures
Psychomotor seizures are a type of focal seizure that primarily affects the dog’s behavior rather than causing physical convulsions. During these seizures, dogs may exhibit odd behaviors, such as:
- Chasing their tail
- Snapping at invisible objects
- Running in circles
- Staring into space
These episodes can last from a few seconds to several minutes and may be mistaken for odd or compulsive behaviors rather than seizures.
Cluster Seizures
Cluster seizures occur when a dog experiences multiple seizures within 24-hours. This type of seizure is particularly concerning as it can be life-threatening and requires immediate veterinary attention. Managing cluster seizures often involves medication adjustments and close monitoring by a veterinarian.
Status Epilepticus
Status epilepticus is a severe and prolonged seizure lasting more than five minutes or a series of seizures without full recovery between them. This condition is a medical emergency and can cause permanent brain damage or even death if not treated promptly.
Immediate veterinary intervention is crucial, and treatment may involve intravenous medications to stop the seizure activity. You could also consult a veterinarian if you want to use medication like Keppra for dogs. Asking for veterinary advice is essential to ensure proper medication.
Manage an Old Dog Seizures Today
Understanding the different types of old dog seizures can help you recognize and respond appropriately to these events. This ensures your furry friend receives the best possible care. If your dog experiences seizures, working closely with your veterinarian is essential to develop a comprehensive management plan tailored to their specific needs.
If you want to read more articles, visit our blog.

 HOME IMPROVEMENT1 year ago
HOME IMPROVEMENT1 year agoThe Do’s and Don’ts of Renting Rubbish Bins for Your Next Renovation

 BUSINESS1 year ago
BUSINESS1 year agoExploring the Benefits of Commercial Printing

 HOME IMPROVEMENT9 months ago
HOME IMPROVEMENT9 months agoGet Your Grout to Gleam With These Easy-To-Follow Tips

 BUSINESS1 year ago
BUSINESS1 year agoBrand Visibility with Imprint Now and Custom Poly Mailers

 TECHNOLOGY12 months ago
TECHNOLOGY12 months agoDizipal 608: The Tech Revolution Redefined

 HEALTH9 months ago
HEALTH9 months agoThe Surprising Benefits of Weight Loss Peptides You Need to Know

 HEALTH9 months ago
HEALTH9 months agoYour Guide to Shedding Pounds in the Digital Age

 HEALTH1 year ago
HEALTH1 year agoHappy Hippo Kratom Reviews: Read Before You Buy!










